Governance & Management of IT
Visual mnemonics for IT governance frameworks, strategy alignment, risk management, and organizational oversight
Alex's Week 2 — The Governance Gap
Alex survived her first week. She knows how to plan an audit and collect evidence. Now her manager drops a bigger challenge: audit IT governance at Meridian Corp. “You'll need to understand how the whole thing is supposed to work,” he says, “before you can tell them how badly it isn't.” Alex opens her notebook to a fresh page.
IT Governance Frameworks
IT Governance Frameworks: "CITI"
Alex sits across from Meridian's CIO and asks the question every governance auditor starts with: “What framework does your IT governance follow?” He pauses. Looks at his bookshelf. “We follow… best practices.” Alex writes in her notebook: No formal framework adopted. This is going to be a long week.
COBIT
IT governance & management framework by ISACA. Focus: business-IT alignment, value delivery, risk management.
ITIL
IT service management best practices. Focus: service lifecycle — strategy, design, transition, operation, improvement.
TOGAF
Enterprise architecture framework. Focus: architecture development method (ADM) for aligning IT with business.
ISO 27001
Information security management system (ISMS) standard. Focus: confidentiality, integrity, availability.
COBIT is the #1 Framework for CISA
COBIT (Control Objectives for Information and Related Technologies) is ISACA's own framework and the most heavily tested. It provides 5 governance principles and distinguishes governance (evaluate, direct, monitor) from management (plan, build, run, monitor).
COBIT is the primary framework referenced by ISACA for IT governance. Know the distinction: Governance is the board's responsibility (evaluate, direct, monitor); Management is the executive team's responsibility (plan, build, run, monitor). The exam frequently tests this separation.
The 2017 Equifax breach was attributed partly to governance failures — the security team reported to the CTO, not the board, creating accountability gaps that let a known Apache Struts vulnerability go unpatched for months. The breach cost $575 million in FTC settlement alone.
Reveal Answer
Reveal Answer
Reveal Answer
Alex now knows Meridian has no framework. But does it at least have an IT strategy? She asks to see it.
IT Strategy & Alignment
IT Strategy Aligned to Business Strategy
Alex asks for the IT strategy document. Someone finds it on a shared drive. Last updated four years ago. Signed by a CEO who left in 2022. The IT department spent $2M building a data warehouse — nobody in the business asked for it. Alex underlines a phrase in the strategy document: “Align IT with business needs.” Ironic.
Business Strategy
- Mission, vision, values
- Business objectives & goals
- Competitive positioning
- Market & stakeholder needs
IT Strategy
- IT mission aligned to business
- Technology roadmap
- IT capabilities & investments
- Service delivery model
IT Balanced Scorecard Links Strategy to Performance
The IT balanced scorecard translates IT strategy into four measurable perspectives: Financial (cost efficiency), Customer (user satisfaction), Internal Processes (operational excellence), and Learning & Growth (innovation & skills).
The IT strategic plan should be a 3–5 year long-range plan aligned to the business strategic plan. The IT tactical plan covers 1 year and breaks down the strategic plan into actionable projects. If asked what should be reviewed FIRST when auditing IT governance, the answer is the IT strategic plan.
Kodak's IT strategy remained focused on film digitisation infrastructure while the business needed digital camera and mobile photo capabilities. The $1B+ IT investment did not align to where the business needed to go — a textbook IT-business misalignment.
Reveal Answer
Reveal Answer
Reveal Answer
An outdated strategy is one thing. But who is supposed to own it? Alex asks who is responsible for IT governance at Meridian. The answer is… complicated.
Roles & Responsibilities
IT Governance Roles & Responsibilities
Alex asks the question that makes everyone uncomfortable: “Who owns IT risk at Meridian?” The CIO points at the CISO. The CISO points at the infrastructure manager. The infrastructure manager points at the CIO. Three people. Three fingers. Nobody pointing at themselves. Alex writes: No clear accountability for IT risk.

Board of Directors
- Ultimate accountability for IT governance
- Approves IT strategy & policies
- Oversees risk appetite
- Ensures value delivery
IT Steering Committee
- Cross-functional oversight body
- Prioritizes IT projects & investments
- Monitors IT performance
- Resolves resource conflicts
CIO (Chief Information Officer)
- Leads IT strategy execution
- Manages IT operations
- Reports to CEO or Board
- Bridges business & technology
CISO (Chief Info Security Officer)
- Owns information security program
- Develops security policies
- Manages security incidents
- Reports to CIO or directly to CEO
Key Separation: Governance vs. Management
Governance (Board)
- Evaluate, Direct, Monitor
- Sets direction and limits
Management (Executives)
- Plan, Build, Run, Monitor
- Executes within boundaries
The Board of Directors has ultimate accountability for IT governance — this is non-delegable. The IT Steering Committee is an advisory/oversight body, not an operational body. The CISO should ideally report independently of the CIO to avoid conflict of interest.
At Enron, the IT risk function reported to business unit heads who had financial incentives to downplay risk. When no single owner was accountable for IT governance, the oversight gaps enabled the fraud to persist.
Reveal Answer
Reveal Answer
Reveal Answer
Nobody owns risk. Nobody owns strategy. But surely, Alex thinks, they at least have policies written down? She opens the document repository.
Policies, Standards, Procedures & Guidelines
IT Policy Hierarchy
Alex opens the shared drive and finds 47 IT-related documents. None reference each other. Some call themselves “policies.” One is clearly someone's working notes with “POLICY” typed at the top in bold. Another “standard” is actually a guideline. Alex starts sorting them into a hierarchy. It takes the rest of the morning.
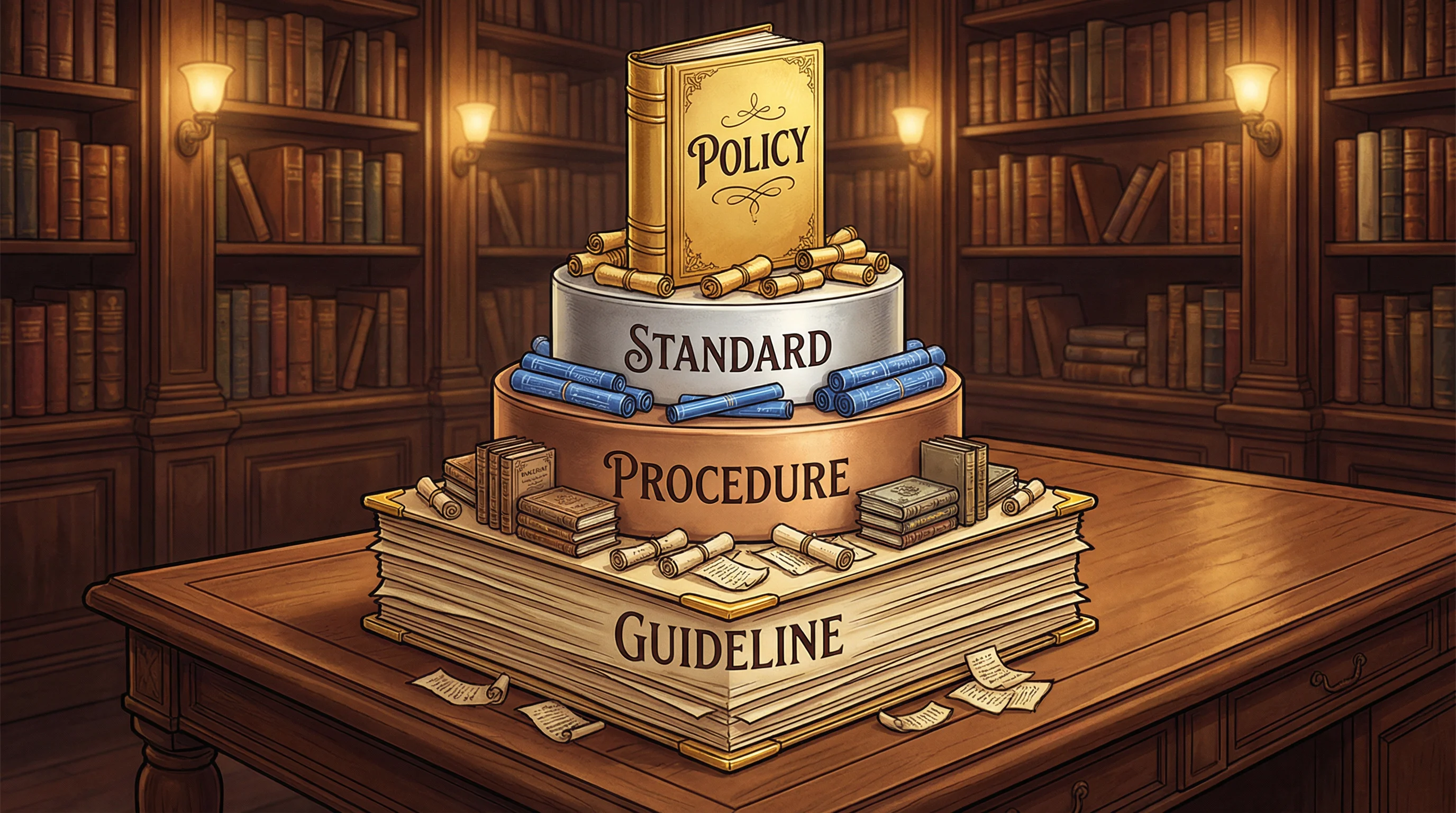
Mandatory Documents
- Policy — Senior management approved
- Standard — Specific requirements
- Procedure — Detailed steps
Optional Document
- Guideline — Best practices, advisory
- Can be deviated from with justification
- Most flexible document type
Only guidelines are optional — policies, standards, and procedures are all mandatory. Policies must be approved by senior management. When the exam asks what to check FIRST for governance issues, start with whether an up-to-date policy exists.
The 2013 Target breach was enabled partly by inadequate vendor access policies — a third-party HVAC vendor had network access that wasn't governed by appropriate policy controls. Target paid $18.5M in state settlement.
Reveal Answer
Reveal Answer
Reveal Answer
Policies are a mess. But at least Meridian tracks its risks… right? Alex asks to see the risk register.
Risk Management
IT Risk Management Process
The risk register exists. Alex finds it in a dusty folder on the infrastructure manager's desk. Last reviewed eighteen months ago. Item #1: “Legacy system failure — HIGH.” No action taken. No owner assigned. Alex asks why. “We've always managed,” says the infrastructure manager. Alex writes: Risk register exists but is not actively managed.

Identify
Catalog threats, vulnerabilities, and assets
Assess
Analyze likelihood × impact. Quantitative or qualitative.
Respond
Choose: avoid, transfer, mitigate, or accept
Monitor
Ongoing tracking, KRIs, risk register updates
🚫 Avoid
Eliminate the risk by stopping the activity entirely
🤝 Transfer
Shift to a third party (insurance, outsourcing)
🛠️ Mitigate
Reduce likelihood or impact with controls
✋ Accept
Acknowledge & absorb. Must be approved by management.
Risk Appetite vs. Risk Tolerance
Risk Appetite — The broad level of risk the organization is willing to accept to achieve its objectives. Set by the Board.
Risk Tolerance — The acceptable variation from the risk appetite. More specific and measurable.
Risk acceptance requires formal approval by senior management — it cannot be decided by IT alone. The risk register should be updated continuously, not just annually. Know the difference between qualitative (high/medium/low) and quantitative (ALE = ARO × SLE) risk analysis.
Knight Capital Group (2012) had a risk register entry about its legacy trading system. The risk was not actioned. A faulty software deployment activated the dormant system, and within 45 minutes, Knight lost $440 million.
Reveal Answer
Reveal Answer
Reveal Answer
The risks are known but ignored. Alex wonders: if nobody is managing risk, who is managing the IT resources? She pulls the asset inventory.
IT Resource Management
The Four IT Resources
Alex pulls the IT asset inventory and finds something remarkable. Meridian has three separate project management systems. Three different departments bought their own without checking what already existed. Nobody knows which one is the “official” system. Annual licence cost for the duplicates: $340,000. Alex writes: No central resource governance.

People
- Skills & competencies
- Training programs
- Succession planning
- Segregation of duties
Infrastructure
- Hardware & networks
- Data centers
- Cloud services
- Capacity planning
Applications
- Business software
- Enterprise systems
- Custom development
- License management
Information
- Data classification
- Data lifecycle
- Data quality
- Data governance
Resource Optimization Goal
IT resource management ensures that the right resources are available at the right time to support business objectives. The IS auditor should verify that resources are inventoried, managed, and optimized through proper planning and monitoring.
Human resources are often the most critical and vulnerable IT resource. The exam frequently tests mandatory vacations, job rotation, and segregation of duties as key HR controls. Data classification is the foundation of information resource management.
The UK's NHS experienced system conflicts during the WannaCry ransomware attack (2017) partly because different trusts ran incompatible legacy systems with no central resource governance. 80 NHS trusts were affected.
Reveal Answer
Reveal Answer
Reveal Answer
Three systems doing one job. Zero coordination. But surely the performance dashboard would have flagged this? Alex checks the KPIs.
IT Performance Management
KPIs, KRIs & the Balanced Scorecard
The KPI dashboard looks beautiful. Bright green: 98% uptime. Alex is almost reassured — until she pulls the actual incident logs. Twenty-three outages last month. They weren't counted because they were classified as “planned maintenance.” The dashboard is measuring what makes management comfortable, not what matters. Alex writes: KPIs do not reflect operational reality.
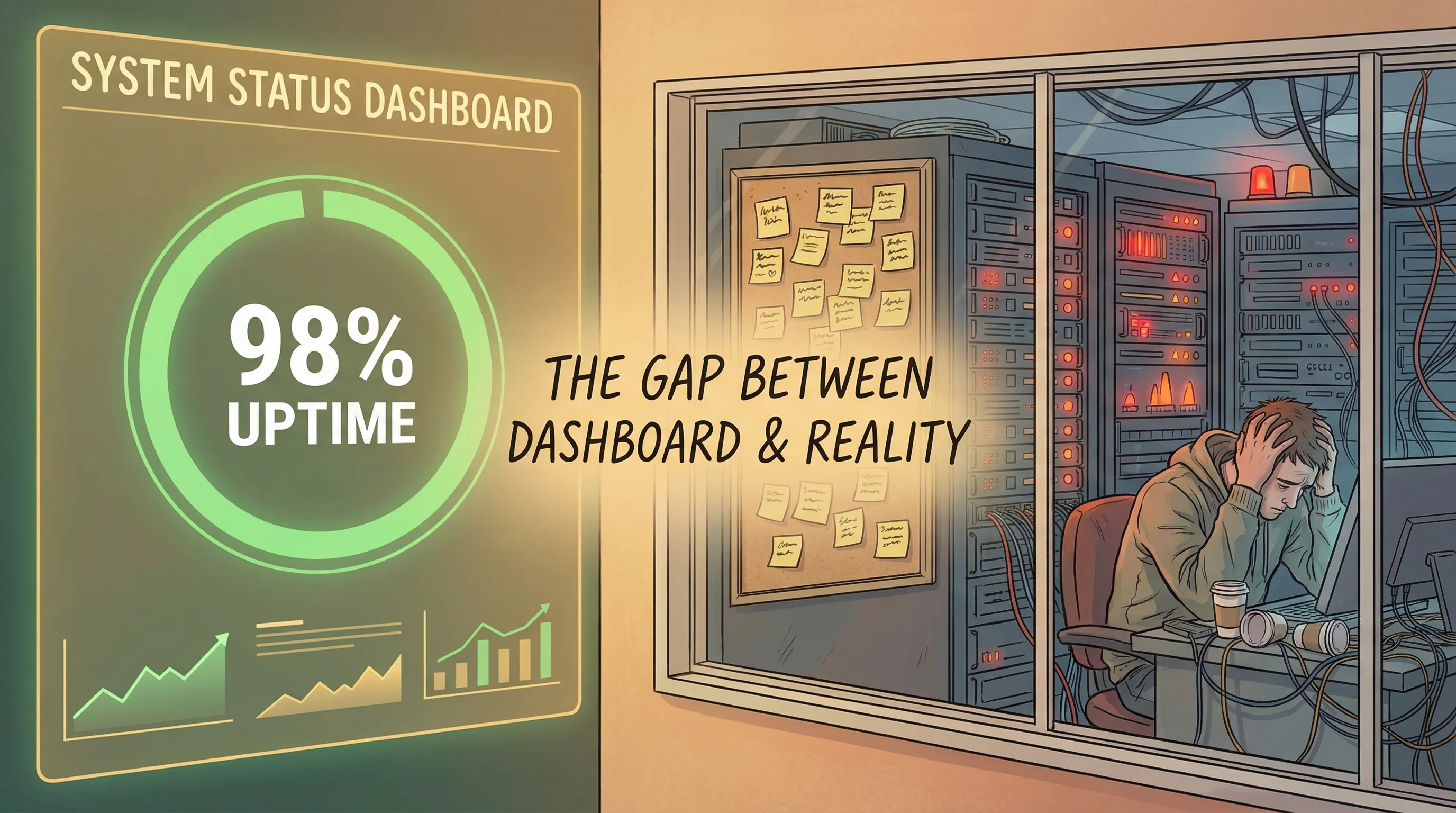
KPIs (Key Performance Indicators)
- Measure performance against goals
- Lagging indicators — what happened
- Example: system uptime %, project on-time delivery
KRIs (Key Risk Indicators)
- Early warning signals of risk
- Leading indicators — what could happen
- Example: failed login attempts, overdue patches
💰 Financial
Cost efficiency, IT budget variance, ROI on IT investments
😊 Customer
User satisfaction, SLA adherence, service quality
⚙️ Internal Process
System uptime, incident resolution time, change success rate
📚 Learning & Growth
Staff certifications, training hours, innovation projects
Benchmarking
Comparing IT performance against industry peers, best practices, or internal historical data. Types: Internal (within the org), External/Competitive (against peers), Functional (against best-in-class processes regardless of industry).
Know the difference: KPIs are lagging (measure past performance), KRIs are leading (warn of future risk). The balanced scorecard translates strategy into measurable objectives across four perspectives. Benchmarking against industry peers is an external benchmark.
The Boeing 737 MAX crisis involved KPIs that measured on-time delivery but not safety gate compliance. When performance metrics don't measure what matters, organisations optimise for the wrong outcomes.
Reveal Answer
Reveal Answer
Reveal Answer
The metrics are lying. But where does the money go? Alex turns to the IT budget — and finds a process that would make any auditor wince.
IT Investment & Budgeting
IT Investment Analysis Methods
Alex maps out Meridian's IT budget process. Department heads submit wish lists in November. The CFO cuts everything by 30%. IT rebuilds the same requests in January. No ROI analysis. No TCO calculation. No prioritisation framework. The most expensive project last year was approved because the VP who requested it “was very insistent.” Alex writes: No formal investment analysis methodology.

TCO (Total Cost of Ownership)
Full lifecycle cost: acquisition + operation + maintenance + retirement. Includes hidden costs like training and support.
ROI (Return on Investment)
Measures profitability: (Net Benefits / Cost) × 100%. Higher ROI = better investment.
NPV (Net Present Value)
Present value of future cash flows minus initial investment. Accounts for time value of money. Positive NPV = good.
Cost-Benefit Analysis
Compare total costs vs. total benefits. Include tangible & intangible factors. Benefits must exceed costs.
IRR (Internal Rate of Return)
The discount rate that makes NPV = 0. Projects with IRR greater than the cost of capital (hurdle rate) are typically approved. Also know payback period — time to recoup the investment.
NPV is the most reliable method because it accounts for the time value of money. A positive NPV means the project adds value. TCO gives the most complete picture of total costs. The IT Steering Committee typically prioritizes projects based on these financial metrics aligned with strategic goals.
The FBI's Virtual Case File project (2005) was cancelled after spending $170 million because investment decisions were made without proper business case analysis, requirements management, or ROI framework.
Reveal Answer
Reveal Answer
Reveal Answer
No investment discipline. Alex is starting to see a pattern. She now turns to the vendors — and finds something that keeps her up that night.
Vendor & Third-Party Management
Vendor Management Lifecycle
Alex reviews the vendor contracts and her stomach drops. Meridian's most critical system — the one processing all customer transactions — is hosted by a vendor whose contract expired eight months ago. They're operating month-to-month. No SLA is currently enforceable. The vendor knows it. Alex writes in capitals: CRITICAL SYSTEM ON EXPIRED CONTRACT. NO ENFORCEABLE SLA.

Selection
RFP, due diligence, vendor evaluation
Contract
SLAs, terms, right-to-audit clause
Monitor
SLA compliance, performance reviews
Renew/Exit
Renegotiate or transition plan
SLAs (Service Level Agreements)
- Define measurable service levels
- Uptime guarantees (e.g., 99.9%)
- Response & resolution times
- Penalties for non-compliance
Key Contract Clauses
- Right-to-audit — Essential for IS auditor
- Data ownership — Org retains ownership
- Exit strategy — Data return/destruction
- Liability & indemnification
Vendor Risk Management
Outsourcing transfers execution, not accountability. The organization remains responsible for data protection and compliance. Perform ongoing vendor risk assessments, especially for critical vendors. Review SOC reports (SOC 1, SOC 2) for assurance on vendor controls.
The right-to-audit clause is the most critical contractual element for an IS auditor. Without it, the auditor cannot verify vendor controls. Outsourcing does NOT transfer accountability — the organization remains ultimately responsible. SOC 2 Type II reports provide the most assurance over a period.
The 2013 Target breach entry point was a third-party HVAC vendor with network access governed by an expired contract with no current SLA. Third-party risk management is only effective when contracts are current and SLAs are enforceable.
Reveal Answer
Reveal Answer
Reveal Answer
Expired contracts, no SLAs. Alex needs a way to summarise just how bad Meridian's governance is. She reaches for a maturity model.
Maturity Models
CMM Maturity Levels (0–5)
Alex maps Meridian's IT governance against the maturity model. Level 1. Maybe. The infrastructure manager disagrees. He thinks they're Level 3 — “We have processes,” he insists. Alex shows him the evidence: no documentation, no consistency, no measurement. He goes quiet. Alex writes: Self-assessed Level 3. Evidence supports Level 1.
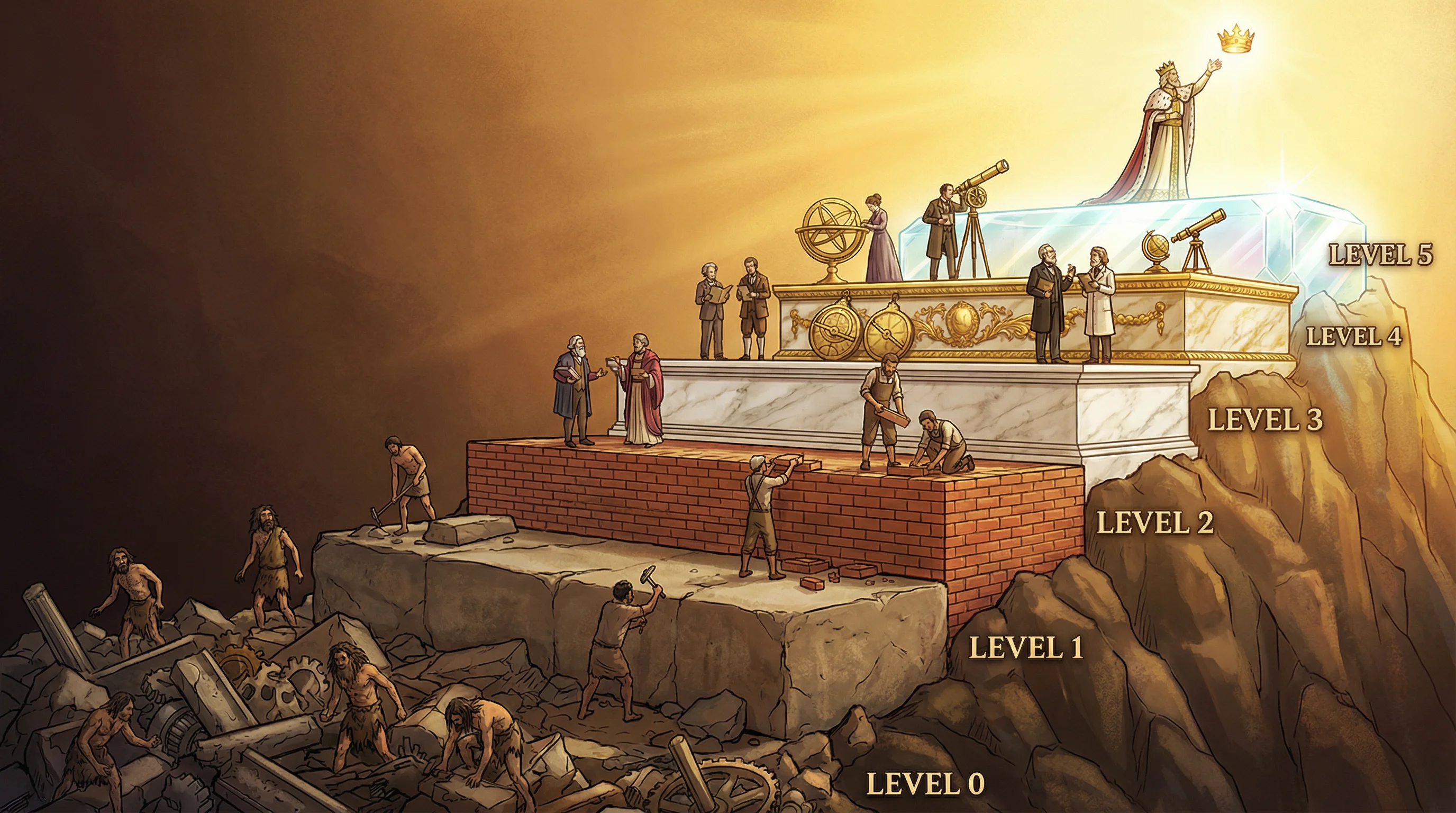
Maturity Model Usage in Auditing
IS auditors use maturity models to assess the current state of IT processes and recommend a target maturity level. Most organizations aim for Level 3 (Defined) as a baseline. Maturity assessments help prioritize improvement efforts and track governance progress over time.
Level 3 (Defined) is the minimum acceptable maturity for most organizations. The key distinction between Level 2 and Level 3 is documentation — at Level 2, processes exist but aren't documented; at Level 3, they are standardized and documented. Not all processes need to reach Level 5.
A 2019 Gartner survey found 87% of organisations rated their IT governance maturity at Level 3 or above. Independent assessments found most were actually at Level 1–2. Self-assessment without evidence is the most common maturity model failure.
Reveal Answer
Reveal Answer
Reveal Answer
Level 1. Alex has the evidence. Now she needs to deliver it properly — through the right channels, to the right people. That's where audit governance comes in.
Audit's Role in IT Governance
IS Auditor: Independent Guardian of Governance
Alex's governance report is ready. She walks it to the IT Steering Committee's desk. It's the first time audit findings have ever gone directly to the committee. The CIO intercepts her in the hallway: “Shouldn't that come to me first?” Alex pauses. “No,” she says. “That would compromise our independence.” The CIO thought audit reported to him.

What the IS Auditor Does
- Evaluates IT governance effectiveness
- Reviews alignment of IT with business
- Assesses risk management practices
- Verifies control design & operating effectiveness
- Reports findings to the Board/Audit Committee
What the IS Auditor Does NOT Do
- Does NOT implement controls
- Does NOT make management decisions
- Does NOT approve transactions
- Does NOT take on operational responsibilities
- Does NOT compromise independence
Independence is Non-Negotiable
The IS auditor must be organizationally independent from the areas being audited. Ideally reports to the Audit Committee of the Board, not to IT management. Independence ensures objectivity and credibility. If independence is impaired, the auditor must disclose this.
The IS auditor's primary role in governance is to provide independent assurance. They should never implement or approve controls — doing so impairs independence. When the exam asks about an auditor's "greatest concern," think about threats to independence and objectivity.
The collapse of Carillion (UK, 2018) was partly attributed to an internal audit function that reported to the CFO rather than the audit committee. Audit findings about cash flow and contract risk were not escalated independently.
Reveal Answer
Reveal Answer
Reveal Answer
The governance report is delivered. But there's one more thing Alex needs to check: what happens when everything goes wrong? She opens the Business Continuity Plan.
Business Continuity Planning Governance
BCP: Board-Level Oversight of Resilience
Alex opens Meridian's Business Continuity Plan. It looks professional — until she reads the details. The plan references three systems that were decommissioned two years ago. The contact list includes people who no longer work at Meridian. “Nobody told us,” says the BCP owner. Alex writes her final finding: BCP is outdated and untested against current infrastructure.

BCP Governance Responsibilities
Board / Senior Management
- Approve & fund BCP program
- Set recovery priorities
- Review BCP test results
- Ensure adequacy & currency of plans
BCP Coordinator / Team
- Develop & maintain the BCP
- Conduct Business Impact Analysis
- Organize testing & exercises
- Update plans after changes/tests
BIA
Business Impact Analysis — identify critical processes
Strategy
Define recovery strategies & set RTO/RPO
Plan
Document procedures, roles, contacts
Test
Tabletop, simulation, full interruption tests
Maintain
Regular updates after changes or lessons learned
Key Terms
- BIA — Identifies critical processes & impact of disruption
- RTO — Recovery Time Objective (max downtime)
- RPO — Recovery Point Objective (max data loss)
- MTD — Maximum Tolerable Downtime
BCP Testing Types (Least → Most Disruptive)
- Checklist Review — Paper review only
- Tabletop / Walkthrough — Talk through scenarios
- Simulation — Simulated disaster
- Parallel Test — Activate backup while primary runs
- Full Interruption — Shut down primary (riskiest)
The BIA is the first step in BCP development — always. Senior management must approve the BCP and its testing results. A full interruption test is the most thorough but also the most risky. The BCP must be updated whenever significant changes occur (new systems, org changes, after actual incidents).
When Hurricane Katrina struck in 2005, many banks' BCP plans referenced physical backup sites in New Orleans — the same area hit by the hurricane. Plans that aren't reviewed and tested against realistic scenarios fail precisely when needed most.
Reveal Answer
Reveal Answer
Reveal Answer
Alex's governance report lands on the IT Steering Committee's desk.
Twelve findings. Three critical. The CIO reads it in silence. He expected a clean bill of health. What he got was a mirror. “We knew some of this,” he says finally. “We just didn't have it written down.” Alex has learned something important: governance failures are rarely malicious. They're usually just… unwritten. Her job is to write them down.
Top 10 Exam Traps — Domain 2
✓ COBIT is a framework for governance — it provides principles and practices, not a specific implementation recipe
✓ IT strategy must be aligned TO business strategy — the business leads, IT enables
✓ Outsourcing transfers execution, NEVER accountability — management retains ownership of risk
✓ The optimal maturity level depends on business needs — not every organisation needs Level 5
✓ Steering Committee sets strategic direction — operational decisions stay with IT management
✓ Policy = what we will do (high level). Standard = specific mandatory requirement. Procedure = how to do it step by step
✓ KPIs measure what you CHOSE to measure — the trap is measuring activity, not outcomes
✓ Relationship doesn't replace contract — SLAs and accountability must be documented regardless of history
✓ Some IT investments (compliance, security) have no positive ROI by design — use NPV, TCO, or risk reduction metrics instead
✓ Risk acceptance means management consciously decides to live with the risk — it must be documented and periodically reviewed