Protection of Information Assets
Everything Meridian Corp failed to have in place — and everything Alex needs to understand.
Week 5 — Alex and the CEO's Inbox
Monday morning. Alex arrives to find the CISO pacing. The CEO's email account was compromised over the weekend. A phishing email. The attacker spent 48 hours reading emails, forwarding selected messages to an external address, and sending a wire transfer request to Finance that almost got approved. Alex is pulled into the investigation. Domain 5 is everything she needs to understand — and everything Meridian Corp failed to have in place.
The CIA Triad
Confidentiality, Integrity & Availability
Alex stares at the incident timeline on the whiteboard. The attacker read the CEO's emails — confidentiality breached. Modified one email before forwarding it — integrity breached. The CEO was locked out for six hours during remediation — availability breached. Three pillars. All three fell at once.

Confidentiality
Data is accessible only to authorised individuals. Prevents unauthorised disclosure.
- Encryption
- Access controls
- Data classification
Integrity
Data is accurate, complete, and unaltered by unauthorised parties.
- Hashing
- Digital signatures
- Change management
Availability
Systems and data are accessible when needed by authorised users.
- Redundancy & failover
- Backups
- Disaster recovery
When ISACA asks which CIA property was violated, read carefully: data read by an attacker = confidentiality. Data modified = integrity. System taken offline = availability. Encryption protects confidentiality. Hashing protects integrity. Redundancy protects availability. These are different tools for different purposes — the exam tests whether you can match the tool to the property.
The 2017 WannaCry ransomware attack simultaneously breached all three CIA properties: confidentiality (data accessed by attackers), integrity (files encrypted and corrupted), and availability (systems locked). 200,000 systems across 150 countries were affected, including 80 NHS trusts in the UK.
Reveal Answer
Reveal Answer
Reveal Answer
The CEO's emails were read. The first question: who let the attacker in?
Access Control
Access Control Models
Alex pulls up the CEO's account settings. No MFA. Password: eight characters, his name and birth year. The access control policy requires 12-character passwords and MFA for all executives. The policy existed. The enforcement did not. Alex writes: 'Policy without enforcement is a suggestion.'
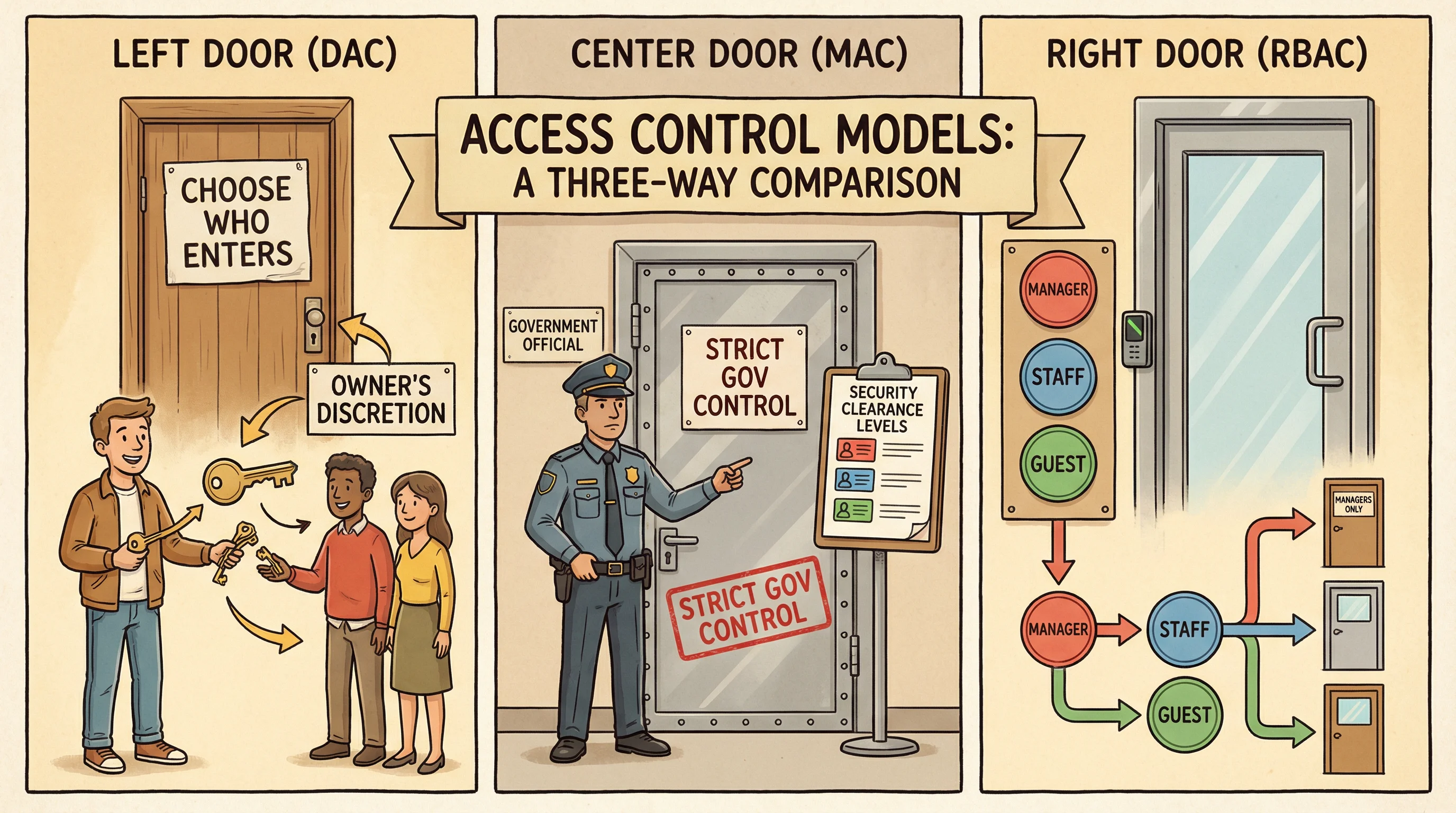
DAC (Discretionary)
Owner decides who gets access. Most flexible, least secure.
- Owner grants permissions
- File sharing, ACLs
- Common in workstations
MAC (Mandatory)
System enforces access based on labels. Most restrictive.
- Classification levels
- Security clearances
- Government/military use
RBAC (Role-Based)
Access determined by job role. Most common in enterprises.
- Roles assigned to users
- Permissions tied to roles
- Easiest to manage at scale
Key Principles
- Least Privilege — Only the minimum access needed to perform the job
- Need-to-Know — Access only the data required for a specific task
- Separation of Duties — No single person controls an entire critical process
- Defense in Depth — Multiple layers of security controls
MAC is the most secure access control model because users cannot override it. RBAC is the most practical for large organisations. DAC is the least secure because the data owner can grant access at their discretion. When the exam asks which model provides the strongest protection, the answer is MAC. When it asks which is most commonly used in enterprises, the answer is RBAC.
The 2021 Colonial Pipeline ransomware attack was enabled by a compromised VPN account with no MFA. The account was for an employee who had left the company — but the account was never disabled. One inactive, unprotected account shut down fuel supply to the US East Coast for 6 days.
Reveal Answer
Reveal Answer
Reveal Answer
The password failed. But how did the attacker get past the login without anyone noticing?
Authentication Methods
Three Factors of Authentication
Alex reviews the authentication logs. The attacker logged in from an IP in Eastern Europe. No geofencing. No anomaly detection triggered. The CEO had logged in from the same Singapore IP every day for three years. The system treated Eastern Europe as normal. One factor. No verification. No alarm.

"K-H-A" — Know it (password), Have it (token), Are it (biometric). True MFA requires factors from at least two different categories, not just two passwords.
Something You Know
- Passwords
- PINs
- Security questions
- Passphrases
Weakest factor — can be guessed or stolen
Something You Have
- Smart cards
- Hardware tokens
- Mobile device (OTP)
- Security keys
Can be lost or stolen physically
Something You Are
- Fingerprints
- Iris/retina scan
- Facial recognition
- Voice patterns
Strongest factor — hardest to forge
Biometric Error Rates
- FRR (Type I) — False Rejection Rate: rejects legitimate user
- FAR (Type II) — False Acceptance Rate: accepts impostor
- CER/EER — Crossover Error Rate: where FRR = FAR
- Lower CER = more accurate biometric system
Two passwords is NOT multi-factor authentication — both are 'something you know.' True MFA combines factors from different categories. The CER (Crossover Error Rate) is the best single metric for biometric accuracy — lower is better. Type II errors (false acceptance) are more dangerous from a security perspective because they let impostors in.
The 2016 LinkedIn breach (2012 breach disclosed in 2016) exposed 117 million passwords, most stored as unsalted SHA-1 hashes — crackable within hours. Strong authentication includes both strong password requirements AND strong storage — both failed.
Reveal Answer
Reveal Answer
Reveal Answer
The attacker got in. Now Alex needs to understand what they could read — and what should have been unreadable.
Encryption & Cryptography
Symmetric vs. Asymmetric Encryption
The emails the attacker read were not encrypted at rest. Wire transfer details — account numbers, amounts, beneficiary names — transmitted in plain text internally. Alex pulls the encryption policy: exists. Encryption implementation: partial. The policy said 'all sensitive data must be encrypted.' Nobody defined what 'sensitive' meant.
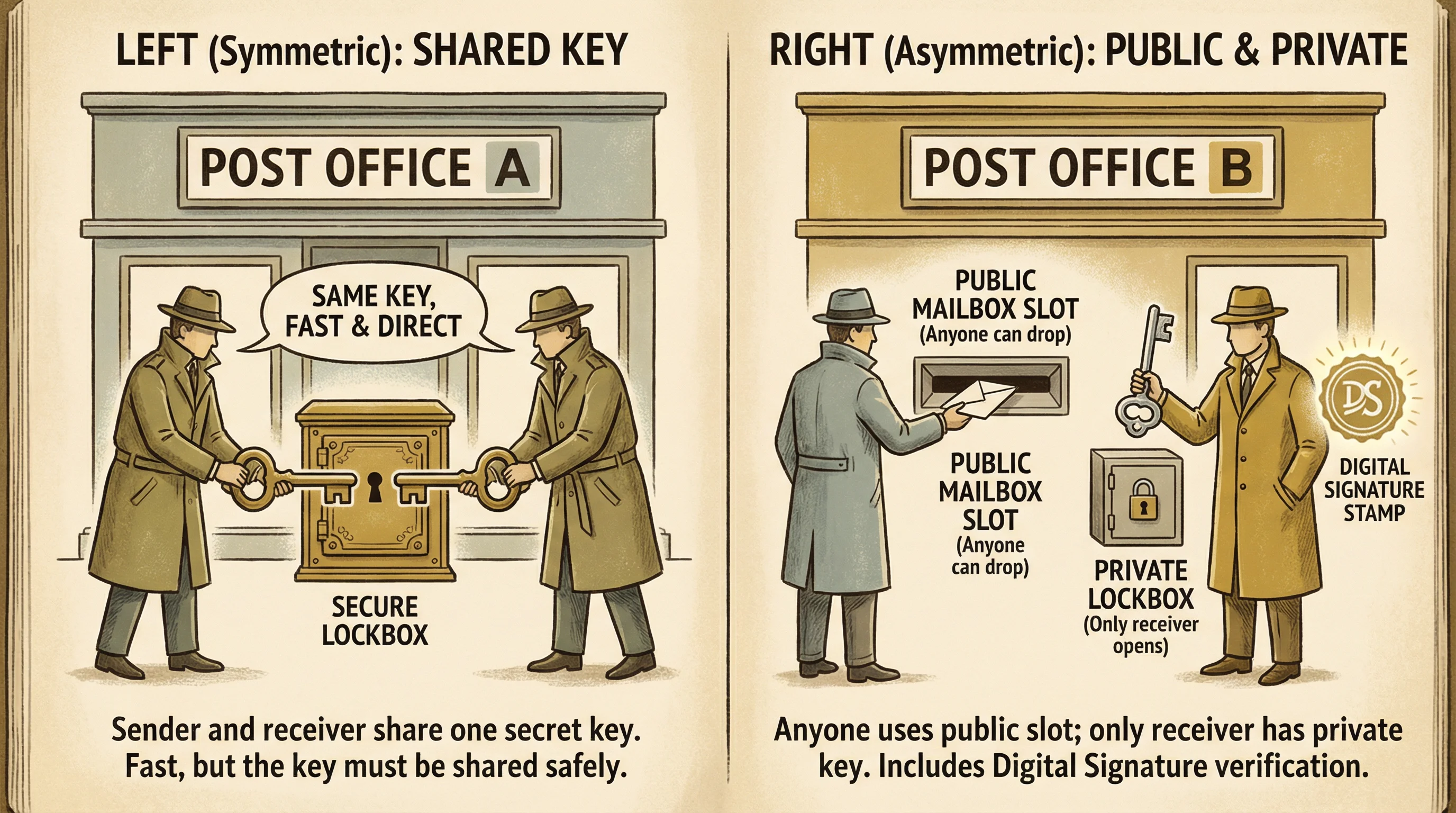
"S = Same key, A = A pair" — Symmetric uses the Same key for both parties (fast but key distribution is hard). Asymmetric uses A pair of keys — one public, one private (slower but solves key distribution).
Symmetric Encryption
One shared key for both encrypt & decrypt
- AES (current standard)
- DES / 3DES (legacy)
- Fast — great for bulk data
- Key distribution is the challenge
Asymmetric Encryption
Public key encrypts, private key decrypts
- RSA, ECC, Diffie-Hellman
- Solves key distribution
- Slower — used for small data
- Enables digital signatures
PKI & Digital Signatures
Digital signatures provide integrity, authentication, and non-repudiation — but NOT confidentiality.
Hashing Algorithms
- MD5 — 128-bit (deprecated, collision-prone)
- SHA-1 — 160-bit (deprecated)
- SHA-256 — 256-bit (current standard)
- SHA-3 — Latest generation
Digital signatures use the sender's private key (not public). The receiver verifies using the sender's public key. Hashing is one-way — you cannot reverse a hash to get the original data. SSL/TLS uses asymmetric encryption for key exchange, then symmetric for bulk data transfer (hybrid approach). Encryption provides confidentiality; digital signatures provide integrity. These are different tools for different purposes.
In 2018, Marriott disclosed a breach affecting 500 million guest records, including 8.6 million unencrypted credit card numbers. The data had been sitting in an unencrypted Starwood database since 2014 — four years of exposure that encryption would have mitigated.
Reveal Answer
Reveal Answer
Reveal Answer
The data was readable. Now Alex traces the attacker's exit route — how did the emails leave the building?
Network Security
Network Defense Architecture
Alex checks the firewall logs. The attacker's exfiltration — forwarding emails to an external Gmail address — passed through the email gateway unchallenged. No DLP rule flagged large volumes of emails being forwarded externally. The wall had a gate. The gate was open. Nobody was watching.

Firewalls
- Packet filtering
- Stateful inspection
- Application-layer (WAF)
- Next-gen (NGFW)
IDS (Detects)
- Signature-based
- Anomaly-based
- Passive — alerts only
- NIDS vs HIDS
IPS (Prevents)
- Inline — blocks traffic
- Active response
- Can cause false positives
- Real-time prevention
DMZ (Demilitarised Zone)
Buffer network between the internet and internal network. Hosts public-facing servers (web, email, DNS) while protecting the internal network.
DLP & Proxy Servers
DLP: Monitors and prevents sensitive data from leaving the network. Proxy: Intermediary that filters, caches, and hides internal IPs.
IDS detects but does not block (detective control). IPS prevents and blocks (preventive control). The exam frequently tests this distinction. A stateful firewall tracks connections and is more secure than basic packet filtering. A firewall controls traffic based on rules — it cannot stop encrypted malware, social engineering, or attacks that use allowed ports. It is one layer, not the whole defence.
The 2013 Target breach used the HVAC vendor's network access to reach the point-of-sale network. Proper network segmentation — a firewall rule separating vendor access from POS systems — would have contained the breach. Target paid $18.5 million in settlement.
Reveal Answer
Reveal Answer
Reveal Answer
The digital defences failed. But Alex is about to discover the physical ones are even worse.
Physical Security
Physical Security Controls
While investigating, Alex discovers the server room door propped open with a fire extinguisher for 'ventilation.' Three people who don't work in IT have a key. The CCTV above the server room has been offline for six weeks. Nobody noticed. Physical security is the foundation. Meridian's foundation has a crack.
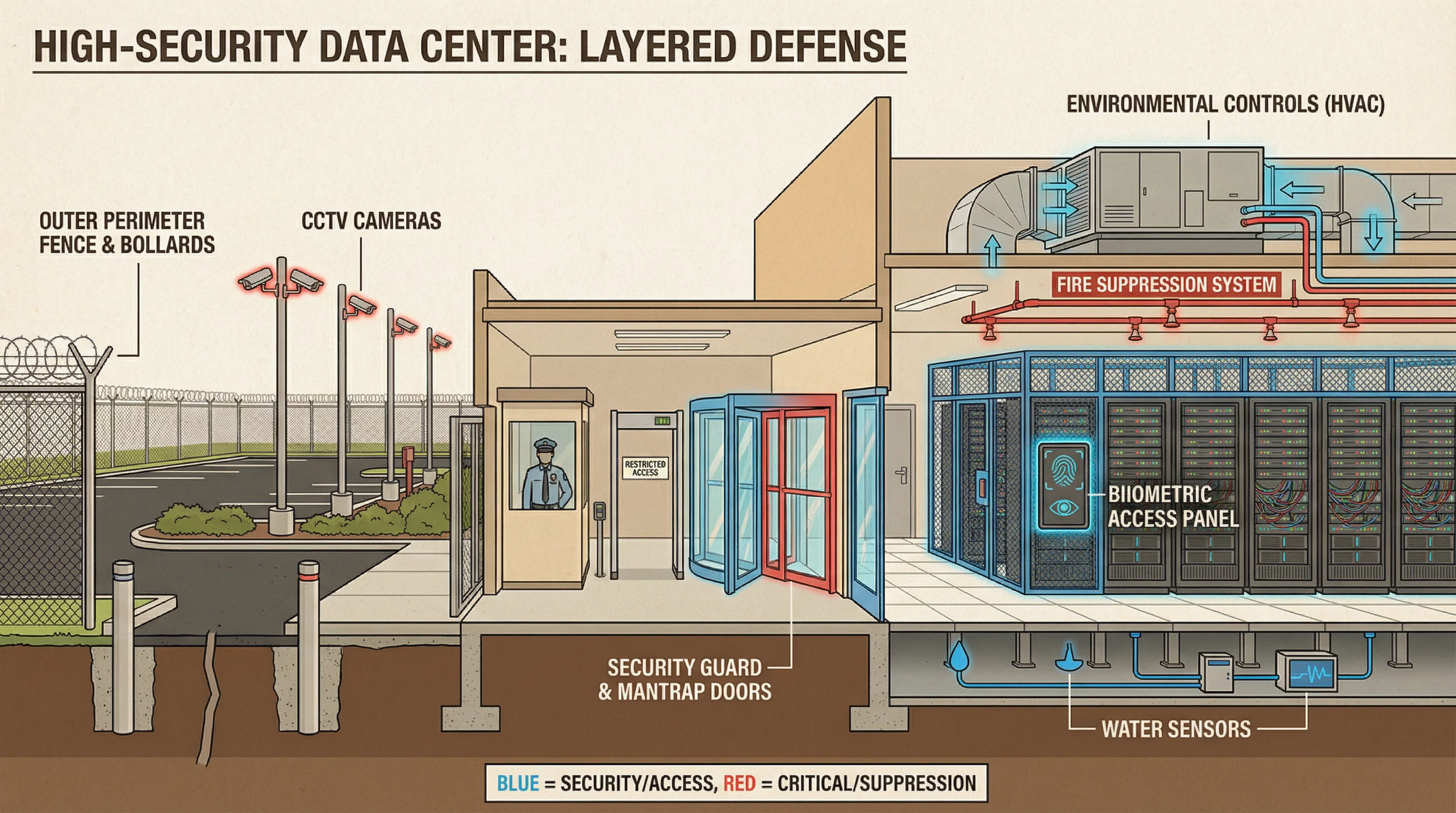
Environmental Controls
- HVAC — temperature & humidity
- Fire suppression (FM-200, inert gas)
- Water/leak detection sensors
- UPS & backup generators
Monitoring Controls
- CCTV with recording & retention
- Motion detectors
- Security guard patrols
- Visitor logs & badge systems
A man-trap (airlock) is the strongest physical access control for preventing tailgating — only one person enters at a time. Water-based sprinklers damage equipment; prefer FM-200 or inert gas suppression for data centres. The IS auditor should verify that physical access logs are reviewed regularly and that CCTV is operational.
In 2008, a thief walked into a Société Générale data centre by tailgating an employee through a secured door. Physical security controls — mantrap, badge-only access, CCTV — exist precisely because insider threats often begin with physical access.
Reveal Answer
Reveal Answer
Reveal Answer
The physical security was an embarrassment. But the original attack wasn't physical — it was psychological.
Malware & Threats
Types of Malware & Social Engineering
The phishing email that compromised the CEO had no malware. Zero. It was a pure social engineering attack — a convincing email from 'IT Support' asking him to verify his credentials. The email gateway scanned for malware. It found none. Because social engineering has no signature. No payload. Just persuasion.
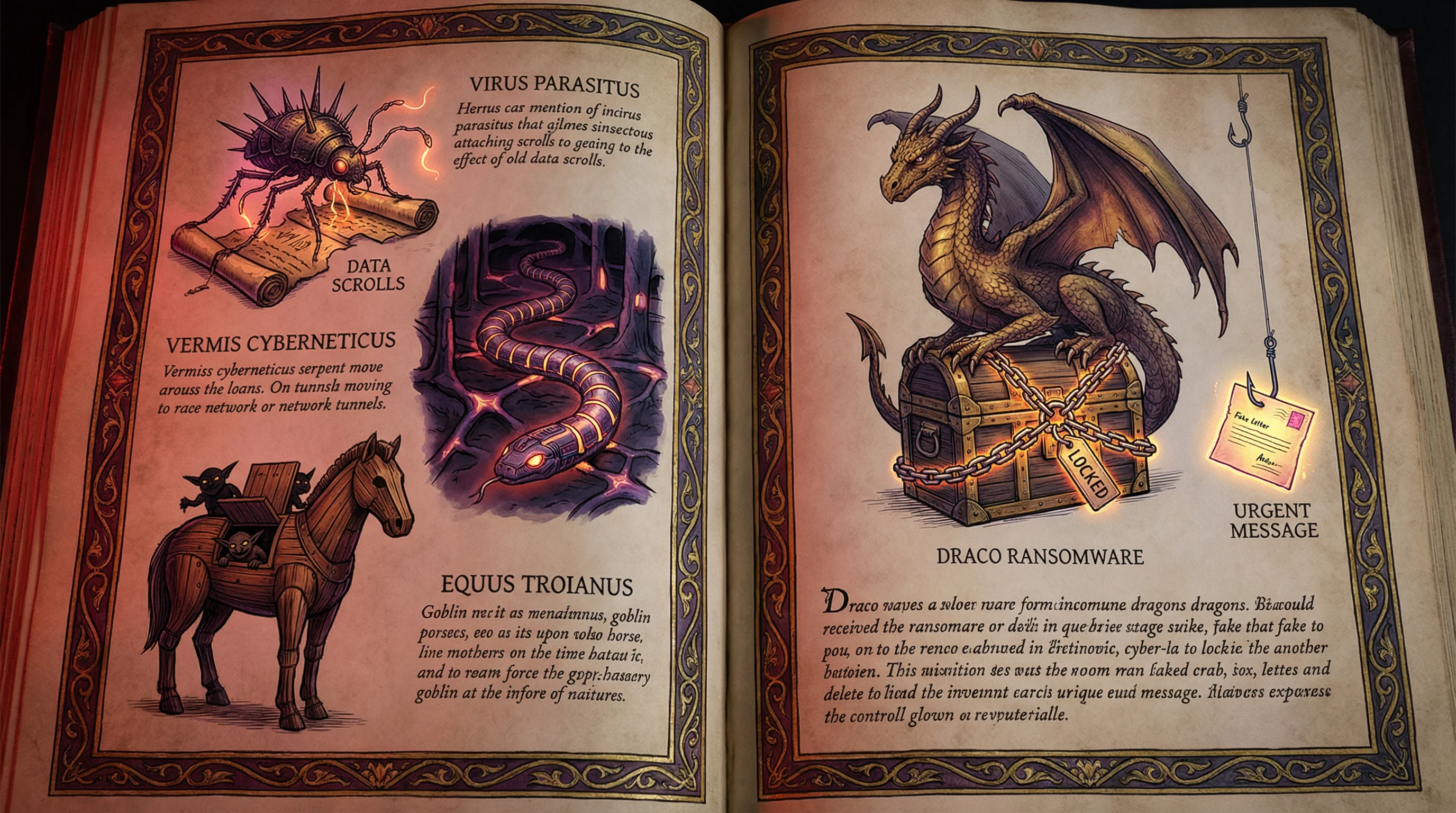
Virus
Attaches to host files. Requires user action to spread. Modifies programs.
Worm
Self-replicating. No host needed. Spreads across networks automatically.
Trojan
Disguised as legitimate software. Opens backdoors. Does not self-replicate.
Ransomware
Encrypts victim's data and demands payment for decryption key. Prevention: regular backups, user training, patching.
Social Engineering
- Phishing — Fake emails/sites to steal credentials
- Spear phishing — Targeted at specific individuals
- Pretexting — Creating a fabricated scenario
- Tailgating — Following authorised person through door
A worm is the most dangerous self-propagating malware because it spreads without user action. The key distinction: viruses need a host, worms don't. For ransomware, the best recovery strategy is tested offline backups. Social engineering attacks are best countered by security awareness training, not technical controls. No antivirus can stop an employee from willingly entering their password.
The 2016 Bangladesh Bank heist netted $81 million through pure social engineering — fraudulent SWIFT payment instructions with no malware. The attackers had studied Bangladeshi banking communication patterns for months. No antivirus would have stopped it.
Reveal Answer
Reveal Answer
Reveal Answer
The attacker used persuasion, not code. But the system they attacked had known weaknesses nobody fixed.
Vulnerability Management
Vulnerability Assessment, Pen Testing & Patching
Alex pulls the vulnerability scan report. The email server has three unpatched vulnerabilities, two rated HIGH. The patch was available three months ago. The patching SLA requires HIGH vulnerabilities to be patched within 30 days. Ninety days. Three times over the deadline. The doctor diagnosed the disease. Nobody administered the cure.
Discover
Identify assets and scan for vulnerabilities
Prioritise
Rank by severity (CVSS) and business impact
Remediate
Apply patches, update configs, or accept risk
Verify
Rescan to confirm fixes are effective
Vulnerability Assessment
Automated scanning to identify weaknesses. Non-invasive. Produces a list of vulnerabilities ranked by severity.
Finds the doors — doesn't try to open them
Penetration Testing
Simulated attack to exploit weaknesses. Invasive. Proves real-world impact. Requires written authorisation.
Tries to open the doors and walk in
Patch Management Process
Penetration testing requires written management authorisation before starting — this is non-negotiable. Vulnerability assessments are broader (find all weaknesses); pen tests are deeper (prove exploitability). Patches should always be tested in a non-production environment before deployment. Vulnerability assessment identifies and classifies. Penetration testing actively exploits. They are NOT the same.
The 2017 Equifax breach exploited Apache Struts CVE-2017-5638, a vulnerability for which a patch had been available for 2 months. Equifax's internal scan flagged it. The patching SLA was not followed. 147 million people's data was exposed.
Reveal Answer
Reveal Answer
Reveal Answer
The vulnerabilities were known. The patches were available. The response was too slow. What about the response to the actual attack?
Security Incident Response
SIEM, Forensics & Chain of Custody
The CISO's incident response was swift on containment — account locked, password reset, forensics engaged. But the chain of custody for the forensic evidence was broken: three people accessed the CEO's laptop before the forensic image was taken. Alex watches from the side. Her job is to observe and document, not participate. Independence matters — even in a crisis.

Preparation
Plan, team, tools, procedures
Identification
Detect & confirm the incident
Containment
Limit the damage & scope
Eradication
Remove the root cause
Recovery
Restore normal operations
Lessons Learned
Post-incident review
SIEM
Security Information and Event Management. Aggregates logs from all systems, correlates events, and generates real-time alerts.
- Centralised log management
- Real-time correlation
- Compliance reporting
Digital Forensics
Preserving and analysing digital evidence for investigation.
- Create forensic image (bit-by-bit copy)
- Work on copy, never original
- Document everything
Chain of Custody Requirements
- Who collected the evidence
- When it was collected
- Where it was stored
- Who had access at each transfer
- What changes (if any) were made
- Unbroken chain = admissible in court
The first priority during an incident is containment (after identification). Evidence preservation is critical — always create a bit-by-bit forensic copy and work on the copy, never the original. If chain of custody is broken, evidence may be inadmissible in court. The auditor's role in incident response is to observe and document, not participate in operational response. Participation compromises independence.
The 2013 Target breach persisted for 16 days after the security team received FireEye alerts — because the incident response process didn't have clear escalation criteria for acting on alerts. Detection without response is not security.
Reveal Answer
Reveal Answer
Reveal Answer
The response was fast but messy. Now Alex asks the harder question: why was this data so easy to steal?
Data Classification
Data Classification Levels
The emails the attacker read included board minutes, M&A discussions, and personal employee data. None of it was classified. If it had been classified as Confidential or Restricted, DLP controls would have triggered on exfiltration. Without classification, every email looked the same to the system. Top secret and lunch orders — all treated equally.
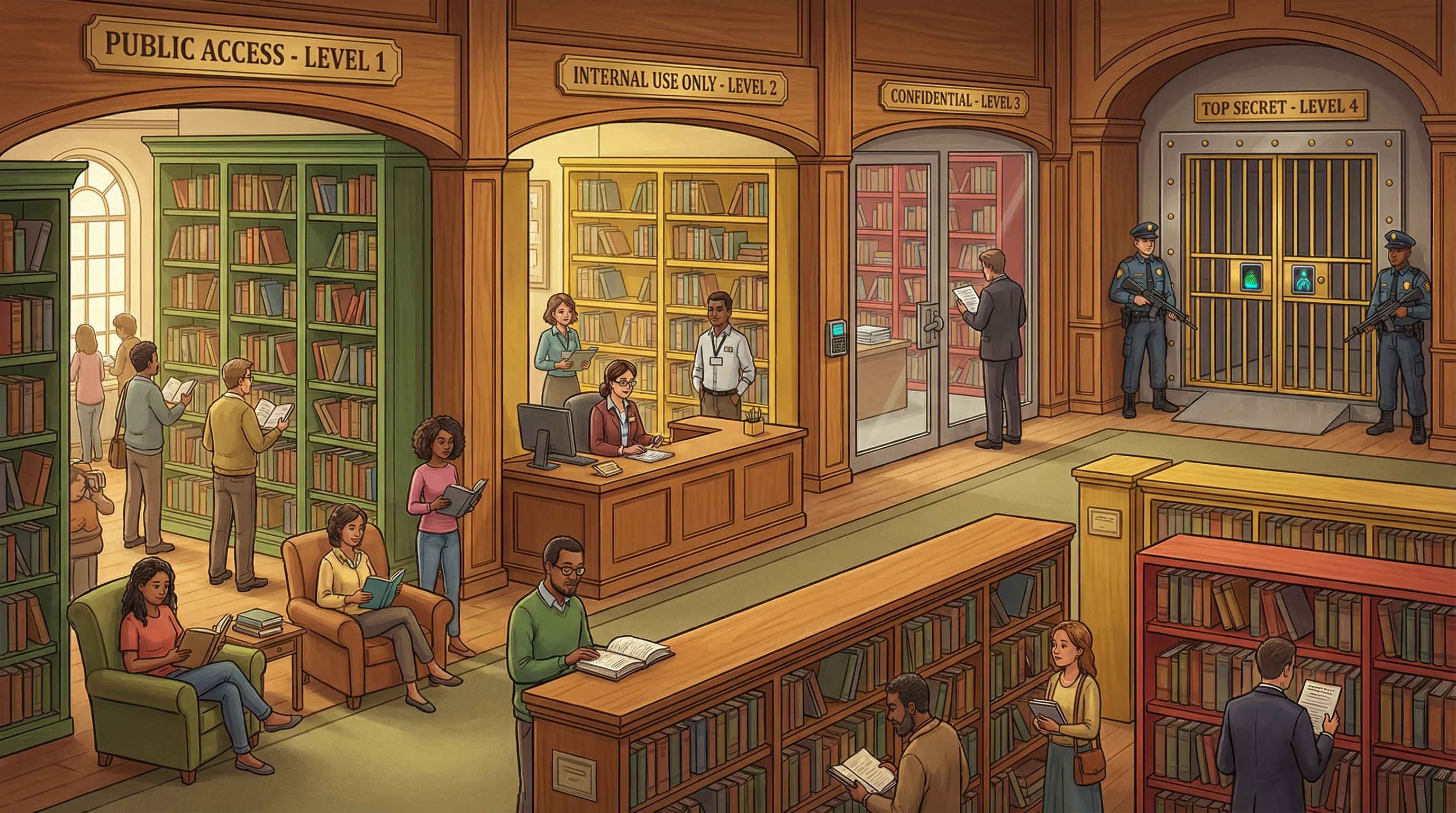
"PICS" — Public (open shelves), Internal (behind the desk), Confidential (locked room), Secret/Top Secret (the vault). Each level up = stricter controls, fewer people with access.
Data Owner (Senior Management)
- Determines classification level
- Defines who can access the data
- Ultimately responsible for data protection
Data Custodian (IT Department)
- Implements controls defined by owner
- Manages backups and storage
- Day-to-day technical safeguards
The data owner (business management) determines classification — NOT IT. The data custodian (IT) implements controls. This distinction is heavily tested. Data classification is a business responsibility. Without classification, DLP controls cannot be calibrated, and staff do not know how to handle sensitive data.
The 2014 Sony Pictures breach exposed classified internal documents — executive emails, salary data, unreleased films — because Sony had no data classification system. Without classification, DLP controls cannot be calibrated, and staff don't know how to handle sensitive data.
Reveal Answer
Reveal Answer
Reveal Answer
The data was unclassified and unprotected. But some of it triggers legal obligations that nobody at Meridian has considered.
Privacy & Compliance
GDPR, Data Protection & Privacy by Design
The breach included personal data of employees — salary information, performance reviews forwarded in emails. Under PDPA (Singapore) and GDPR (for EU employees), this is a notifiable breach. Meridian has 72 hours from discovery to notify. The clock started when the CISO confirmed the breach. It is already ticking. Alex checks: nobody has started the notification process.

Lawfulness
Data must be processed lawfully, fairly, and transparently.
Purpose Limitation
Collected for specified, explicit, and legitimate purposes only.
Data Minimisation
Only collect what is adequate, relevant, and necessary.
Accuracy
Personal data must be accurate and kept up to date.
Storage Limitation
Kept only as long as necessary for the stated purpose.
Integrity & Confidentiality
Appropriate security measures to protect personal data.
Data Subject Rights (GDPR)
- Right to access
- Right to rectification
- Right to erasure ("right to be forgotten")
- Right to data portability
- Right to object to processing
Key Roles & Requirements
- Data Controller — Determines purpose & means of processing
- Data Processor — Processes data on behalf of controller
- DPO — Data Protection Officer (mandatory for some orgs)
- 72-hour breach notification requirement
Under GDPR, the data controller bears primary responsibility, not the processor. Breach notifications must be made within 72 hours. Know the difference between Privacy by Design (building privacy in from the start) and Privacy by Default (strictest settings are the default). The "right to be forgotten" means data subjects can request deletion of their personal data.
British Airways was fined £20 million by the UK ICO for a 2018 breach affecting 400,000 customers. The fine reflected failure to implement appropriate technical measures — encryption, access controls, and monitoring — not just the breach itself.
Reveal Answer
Reveal Answer
Reveal Answer
The legal clock is ticking. But how did this all start? One click. One person. One moment of inattention.
Security Awareness Training
The Human Element & Training Programs
Alex interviews the CEO. He received the phishing email on his phone, was in a hurry, and clicked without thinking. 'I thought it was real,' he says. The last security awareness training at Meridian Corp was 18 months ago. It was a 20-minute video. Nobody checked if anyone watched it. The strongest firewall cannot stop a CEO in a hurry.
"People are the weakest link" — The strongest firewall cannot stop an employee from clicking a phishing link. Technical controls protect systems; training protects humans. Security is only as strong as its least informed user.
Awareness Program Elements
- New employee orientation security training
- Annual refresher courses
- Simulated phishing campaigns
- Security newsletters & reminders
- Role-specific training for IT staff
Training Must Cover
- Password hygiene & MFA
- Recognising phishing attempts
- Reporting suspicious activity
- Clean desk policy
- Data handling & classification
- Acceptable use policy
Measuring Effectiveness
- Phishing simulation click rates (should decrease over time)
- Number of security incidents reported by employees
- Training completion rates
- Post-training quiz scores
Security awareness training is the most effective control against social engineering attacks. The exam often asks: 'What is the BEST way to prevent phishing?' — the answer is user training, not a technical control. Training should be mandatory, regular, and measured for effectiveness. Security is everyone's responsibility — training must be mandated and monitored by management, not just delivered by IT. Tone from the top matters.
The 2016 US election hack on John Podesta's email began with a phishing email. His IT staffer called it 'legitimate' (he meant 'illegitimate' — a typo). Podesta clicked. No security awareness training, no simulated phishing programme. One click changed the course of an election.
Reveal Answer
Reveal Answer
Reveal Answer
Alex closes the investigation file.
One phishing email. Twelve security failures. Alex's investigation report maps every gap at Meridian Corp: missing MFA, weak passwords, no encryption, no DLP, broken physical security, unpatched vulnerabilities, broken chain of custody, unclassified data, missed notification deadlines, and no effective training. She knows now that information security is not a single control — it is a system. When any part fails, the whole system is exposed. Domain 5 taught her that protection is not a product. It is a practice.
Top 10 Exam Traps — Domain 5
✓ Encryption provides confidentiality. Digital signatures provide integrity. Hashing provides integrity verification. These are different tools for different purposes.
✓ A firewall controls traffic based on rules — it cannot stop encrypted malware, social engineering, or attacks that use allowed ports. It is one layer, not the whole defence.
✓ The auditor maintains independence — they observe and document, but do not participate in operational response. Participation compromises independence.
✓ Passwords alone are 'something you know' — single-factor. MFA combines factors (know + have + are) and is significantly stronger. ISACA strongly prefers MFA in exam scenarios.
✓ Data classification is a BUSINESS responsibility — the business owner determines sensitivity. IT implements controls based on classification.
✓ They serve different purposes. Symmetric is faster (bulk data). Asymmetric is used for key exchange and digital signatures. Neither is universally 'more secure.'
✓ IDS detects and alerts — it is a detective control. Only IPS can actively block. An organisation with only IDS knows it was attacked; it did not prevent the attack.
✓ Security is everyone's responsibility — training must be mandated and monitored by management, not just delivered by IT. Tone from the top matters.
✓ Correct — but ISACA also tests that residual risk must be formally accepted by management. Acceptance without documentation is not acceptable risk acceptance.
✓ Vulnerability assessment identifies and classifies vulnerabilities. Penetration testing actively exploits them to prove impact. Pen testing requires explicit written authorisation.