SteadyCert
Beautiful graphics for every concept in the CISA Review Manual
Meet Alex Chen — Your Guide Through Domain 1
Alex just joined Meridian Corp's internal audit team. It's Day 1. The CISO has handed her a single task: audit the IT department. She's never done this before. Everything in Domain 1 is something Alex discovers, gets wrong, corrects, and learns — in real time. Follow along.
Chapter 1 Overview
Alex stares at her blank audit plan. Forty-seven systems, three weeks, zero experience. Then a senior auditor drops a dog-eared copy of the ISACA standards framework on her desk. "This is your treasure map," he says. "Every answer you need for the next three weeks starts here."

Part A: Planning (1.1–1.4)
- 1.1 Standards & Ethics
- 1.2 Types of Audits
- 1.3 Risk-Based Planning
- 1.4 Types of Controls
Part B: Execution (1.5–1.10)
- 1.5 Project Management
- 1.6 Testing & Sampling
- 1.7 Evidence Collection
- 1.8 Data Analytics
- 1.9 Reporting
- 1.10 Quality Assurance
Domain Weight: 18% (~27 questions)
This domain is the foundation of IS auditing — master the lifecycle and control concepts.
ISACA loves sequencing questions: "What should the auditor do FIRST?" or "Which phase does this activity belong to?" If you see a question about what comes FIRST in an audit, the answer is almost always a planning activity — understanding the business, defining scope, or assessing risk. Never jump to fieldwork or testing.
When Enron collapsed in 2001, investigators discovered that Arthur Andersen's auditors had skipped fundamental audit lifecycle steps — rushing through planning and ignoring red flags during fieldwork. The result: $74 billion in shareholder value was wiped out as the stock collapsed from $90 to near zero, and an entire audit firm ceased to exist.
Reveal Answer
Reveal Answer
Reveal Answer
IS Audit Standards & Ethics
ISACA Standards Framework
Alex is reviewing the vendor list when she freezes. The IT security vendor — the one getting $2M a year — is the lead auditor's brother-in-law. Nobody mentioned it. Alex flips open the ISACA Code of Ethics. Independence isn't optional. It's Standard 1. She has to report this, even if it makes her unpopular on Day 1.

Standards (MUST)
Mandatory requirements for IS audit and assurance professionals. Non-negotiable.
Guidelines (SHOULD)
Guidance on applying standards. Strongly recommended but not required.
Tools & Techniques (MAY)
Examples and procedures for applying standards. Optional reference material.
General
Independence, ethics, competence
Performance
Planning, supervision, evidence
Reporting
Reports, follow-up activities
When the exam says "must," "required," or "mandatory" — the answer involves Standards (not guidelines, not tools). When it says "should" — that's Guidelines. When it says "may" — Tools & Techniques. ISACA tests this hierarchy constantly. If a question asks what happens when an auditor deviates from a Standard vs. a Guideline, remember: deviating from Standards requires justification and disclosure in the report. Deviating from Guidelines does not.
KPMG's South African division collapsed in scandal when auditors failed to maintain independence while auditing the Gupta family's companies, approving transactions they should have flagged. KPMG was forced to resign from Gupta-linked audits, repay R23 million in fees, and saw its head of audit and other senior partners resign in disgrace. The firm's reputation in South Africa was severely damaged.
Alex now knows the rules she has to follow. But rules don't tell her where to look first.
Audit Authority & Independence
The Audit Charter & Independence
Alex needs to review the access control logs on the ERP system, but the IT manager refuses. "You don't have the authority to demand that," he says, arms crossed. Alex pauses — then pulls out the audit charter, approved by the board last quarter. "Actually, I do. Section 3: the IS audit function has unrestricted access to all systems, records, and personnel." The IT manager reads it. Unfolds his arms. Hands over the logs.
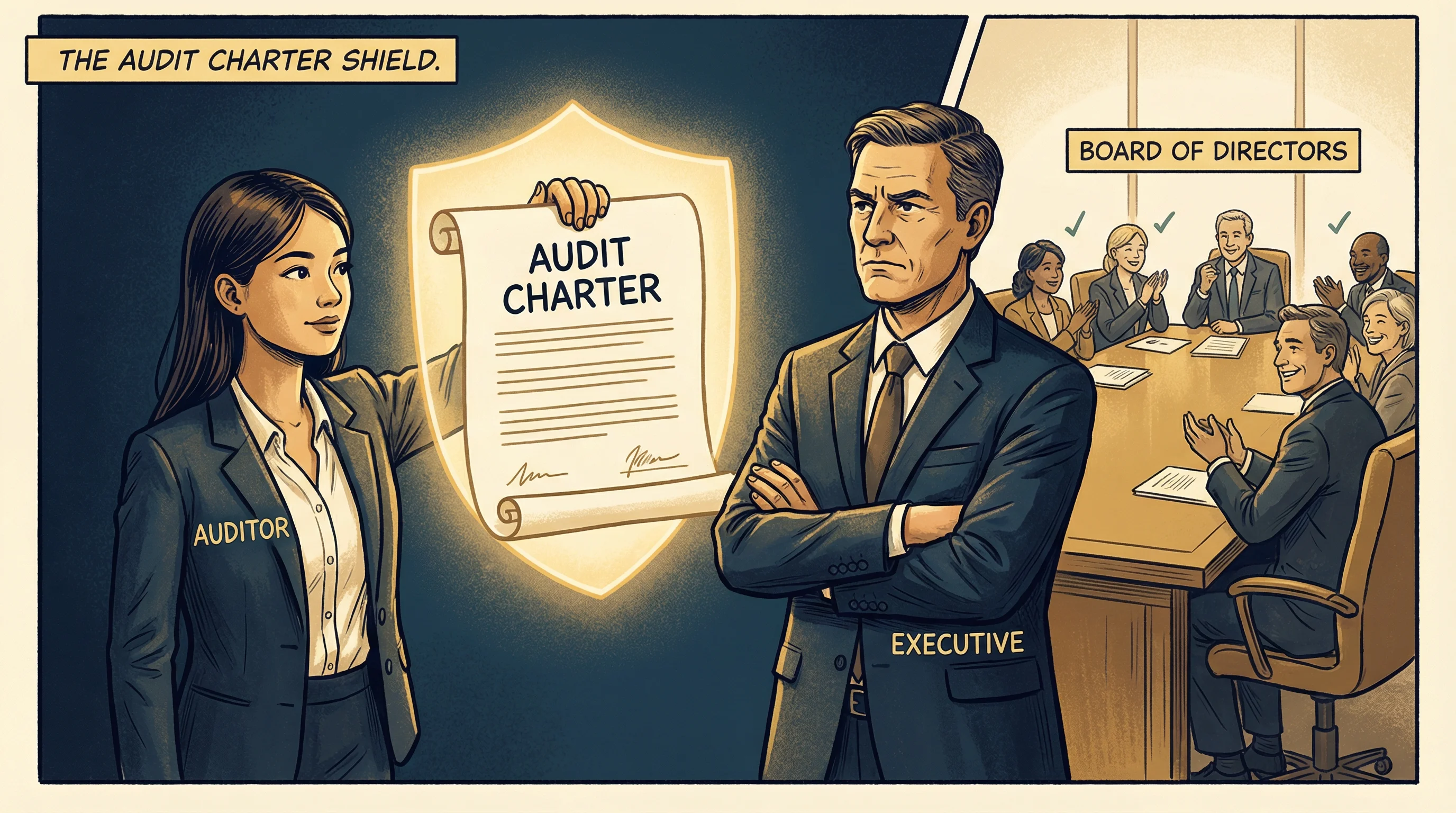
The Audit Charter
The formal document that authorizes the IS audit function. It is the auditor's source of power.
Must Include:
- Purpose of the audit function
- Authority and scope
- Responsibility
- Reporting lines
Critical Exam Point:
- Approved by the board or audit committee
- NOT approved by management
- Management approval = compromised independence
Self-Review
Auditing your own work. Example: auditor designed the control, then audits it.
Self-Interest
Financial stake in the outcome. Example: auditor holds shares in auditee company.
Advocacy
Promoting the client's position. Example: auditor publicly endorses the auditee's product.
Familiarity
Too close to the auditee. Example: auditing a close friend's department.
Intimidation
Being pressured. Example: executive threatens the auditor's job if findings are reported.
Management
Performing management functions. Example: auditor makes decisions on behalf of the auditee.
"Super Scary Auditors Face Intimidating Management"
- Self-review
- Self-interest
- Advocacy
- Familiarity
- Intimidation
- Management
Materiality
The threshold above which a finding must be reported.
- Who sets it? The auditor, based on professional judgment
- What affects it? Risk level, dollar amount, regulatory impact
- Can minor findings be omitted? Not always — aggregated minor findings can become material
Due Professional Care
The auditor must apply the skill and diligence of a reasonably prudent IS auditor.
- Does NOT mean perfection
- Means reasonable care and competence
- ISACA tests: "Was the auditor negligent?" — only if they failed to exercise reasonable care
Three charter questions ISACA always asks: (1) "Who approves the audit charter?" → Board/audit committee, never management. (2) "What establishes the audit function's authority?" → The audit charter. (3) "An auditor previously designed the system being audited — what threat?" → Self-review. If a question describes ANY situation where the auditor's objectivity could be compromised, identify the specific threat type — ISACA wants the precise category, not just "independence issue."
In the Parmalat fraud (Italy, 2003), the internal audit function reported to the CFO — the same person orchestrating the €14 billion fraud. Without a charter establishing independence and direct board reporting, the auditors had no authority and no protection. The fraud went undetected for years.
Reveal Answer
Reveal Answer
Reveal Answer
Types of Audits
Types of Audits
The CISO asks Alex: "Are we doing a financial audit, an operational audit, or an IS audit?" Alex hesitates. Financial checks the numbers. Operational checks efficiency. IS checks the technology controls underneath both. "All three overlap," she realizes. "But my job is the IS layer — making sure the technology itself is trustworthy."

IS Audit
Financial
Operational
Compliance
Forensic
Integrated
When ISACA asks "what type of audit should be performed," pay attention to the goal described in the question. If the goal is "verify adherence to policy" → compliance audit. If the goal is "verify accuracy of financial data" → substantive testing within a financial audit. The trap: "IS audit" is not a type of testing — it's a category that can include both compliance and substantive work.
After the 2013 Target breach that exposed 40 million credit card numbers, investigators found that a compliance audit had given Target a passing grade just months earlier. The compliance audit checked the boxes, but an IS audit focused on network segmentation and vendor access controls would have caught the actual vulnerability.
Control Self-Assessment (CSA)
Alex walks into a conference room expecting to lead a control review. Instead, she finds the IT operations team already mapping their own risks on a whiteboard. "We know where the gaps are," the team lead says. Alex's job isn't to evaluate — it's to facilitate. She sits in the back and takes notes while they assess themselves.
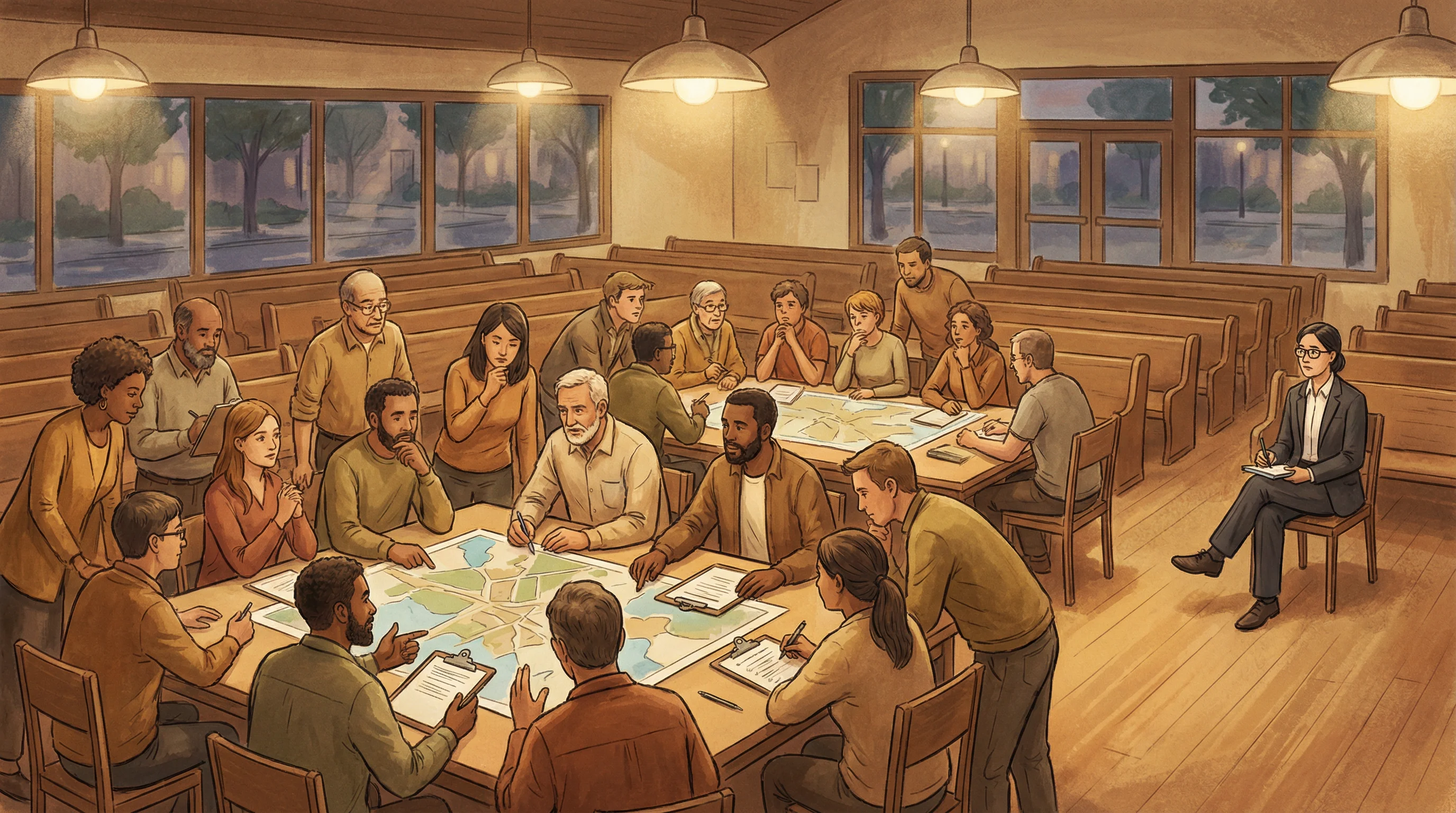
Traditional Audit
- Expert-driven
- Independent assessment
- Periodic schedule
- Formal report output
CSA Approach
- Management/employee-driven
- Collaborative process
- Ongoing assessment
- Self-identified risks
CSA Benefits
- Risk awareness increases
- Early detection of issues
- Management ownership
- Supplements formal audits
IS Auditor Role in CSA: FACILITATOR, not evaluator
The auditor guides the process but does not own the assessment results.
ISACA trap: CSA looks like it replaces the audit. It doesn't. The auditor facilitates but management owns the self-assessment. CSA supplements formal audit — it never replaces it. If a question presents CSA as the ONLY assurance mechanism, that's always wrong. And if the question asks about the auditor's role in CSA, "evaluator" and "assessor" are traps — the answer is "facilitator."
Wells Fargo's fake-accounts scandal (2016) revealed that internal teams had been "self-assessing" their controls as adequate for years — while employees were opening millions of unauthorized accounts. CSA without independent audit oversight became a rubber stamp that hid systemic fraud.
Reveal Answer
Reveal Answer
Reveal Answer
Now she knows what kind of audit she's running. The harder question: where in Meridian Corp does she even start?
Risk-Based Audit Planning
Risk-Based Audit Planning Process
The IT department has 47 systems. Alex has 3 weeks. She can't audit everything. The senior auditor asks: "Which system, if it failed tomorrow, would hurt the company most?" Alex thinks. The payment processing system — it touches revenue, customer data, and regulatory compliance. That's where she starts. Risk-based planning means the scariest fires get the first hose.

Understand Business
Learn the organization's environment and objectives
Identify Audit Universe
Map all auditable areas and processes
Risk Assessment
Evaluate risks for each auditable area
Rank & Prioritize
Order by risk level — high risk first
Develop Plan
Create the formal audit plan document
Allocate Resources
Assign staff, time, and budget
When you see "FIRST" in a Domain 1 question, the answer is almost always about understanding the business or environment — not about starting fieldwork or testing. "What should the auditor do FIRST when planning an IS audit?" → Understand the business environment. Not "identify risks," not "allocate resources," not "start testing." ISACA rewards the auditor who gathers context before acting.
The 2017 Equifax breach exposed 147 million Americans' personal data because the company failed to prioritize patching a known vulnerability in Apache Struts — a system that sat at the top of any reasonable risk ranking. A risk-based audit plan would have flagged this internet-facing system holding SSNs as the highest-priority target.
Reveal Answer
Reveal Answer
Reveal Answer
She knows where to focus. She just doesn't know how much she might miss.
The Audit Risk Model
Alex tests the payroll system and gives it a clean bill of health. Two weeks later, someone finds an unauthorized $50,000 payment that slipped through. Her senior explains: "You can't control the system's complexity or whether management's controls work. But you can control how hard you look. That's detection risk — the only lever you own."

Inherent Risk (IR)
Risk before controls are applied. Driven by the nature of the business and its complexity.
Auditor cannot control
Control Risk (CR)
Can existing controls catch threats? Risk that controls fail to prevent or detect material errors.
Auditor cannot control
Detection Risk (DR)
The only part the auditor directly controls. Quality of audit procedures determines this risk.
Auditor CAN control
Key Relationship
Inverse relationship: Strong controls (low CR) → less detection testing needed (higher acceptable DR). Weak controls → more testing required.
ISACA will present a scenario where something went wrong after the audit and ask which risk component failed. The answer is almost always Detection Risk — because the auditor's procedures didn't catch it. Inherent risk (A) and control risk (B) are properties of the system, not the audit. If the question asks "what can the auditor do to reduce overall audit risk?" — the answer is always about improving detection procedures (more testing, better sampling, CAATs).
The Colonial Pipeline ransomware attack (2021) succeeded partly because an inactive VPN account had no MFA — a control weakness that existed in plain sight. The auditors who reviewed IT controls the previous year gave it a passing grade, their detection procedures insufficient to catch a dormant but dangerous access vector.
Reveal Answer
Reveal Answer
Reveal Answer
She can't eliminate risk — but she can control how hard she looks. Now she needs to know what she's looking for.
Types of Controls
Control Classifications
Alex walks into the server room and the door is wide open. No badge reader, no lock, no sign-in sheet — a missing preventive control. She checks the security camera log: nothing recorded in six months. Detective control, broken too. She writes: "If something went wrong in here, nobody would know until the damage was done."

Preventive
Stop threats before they happen. Shields and locks.
- Access controls
- Encryption
- Segregation of duties
Detective
Identify threats after they occur. Magnifying glass.
- Log monitoring
- IDS/IPS*
- Audit trails
*Note: IPS (Intrusion Prevention System) has both preventive AND detective functions — it can block attacks in real-time (preventive) while also logging them (detective). ISACA may test this nuance.
Corrective
Fix damage after detection. Repair tools.
- Backup restore
- Patch management
- Incident response
Administrative / Management
Policies, procedures, guidelines, risk assessments, security awareness training
Technical / Logical
Software controls: firewalls, encryption, access control lists, authentication
Physical
Tangible controls: locks, guards, CCTV, environmental controls, fencing
ISACA prefers preventive controls, but questions often test whether you know that detective controls are appropriate when prevention isn't feasible. If the question asks what's MISSING and the system already has cameras and alarms — the answer is preventive. But if the question asks "which control is MOST appropriate for detecting unauthorized changes after they occur?" — choosing preventive is the trap. Read what the question is actually asking.
The 2013 Target breach succeeded because a third-party HVAC vendor's credentials gave access to the payment network — a preventive control (network segmentation) was missing entirely. Target had detective controls (FireEye alerts fired), but staff ignored them. When preventive and detective both fail, you're left with corrective — and by then, 40 million card numbers are gone.
Reveal Answer
Reveal Answer
Reveal Answer
She knows what controls should exist. Now she needs to plan how to test them.
Audit Project Management
The Four Audit Stations
It's Week 2 and Alex is behind schedule. Fieldwork is eating all her time — every interview spawns three more questions. Her senior pulls her aside: "You can't cut planning or reporting. If you're behind on fieldwork, narrow the scope and document why. The four phases aren't optional — but the depth within each one is negotiable."

Planning
- Define scope & objectives
- Conduct risk assessment
- Allocate resources
- Develop audit program
Fieldwork
- Gather evidence
- Test controls
- Perform substantive testing
- Document findings
Reporting
- Draft report
- Discuss with management
- Issue final report
- Present findings
Follow-up
- Track remediation
- Verify corrections
- Update risk register
- Conduct follow-up audit
The audit program is developed during planning, not fieldwork. An IS auditor should always discuss findings with management before issuing the final report — giving management a chance to respond is a standard requirement.
The Satyam Computer Services fraud (India's "Enron," 2009) went undetected partly because auditors at PricewaterhouseCoopers rushed through fieldwork and skipped direct bank confirmations during their audit. Cutting corners on one phase cascaded into a $1.47 billion fraud going unreported for years.
Testing & Sampling
Compliance vs. Substantive Testing
Alex faces a fork in the road. The backup policy says backups run nightly. She can check if the policy is being followed (compliance test) or check if the actual backup data is complete and restorable (substantive test). "Both," her senior says. "First check if the control works. If it doesn't, dig deeper into the data itself."
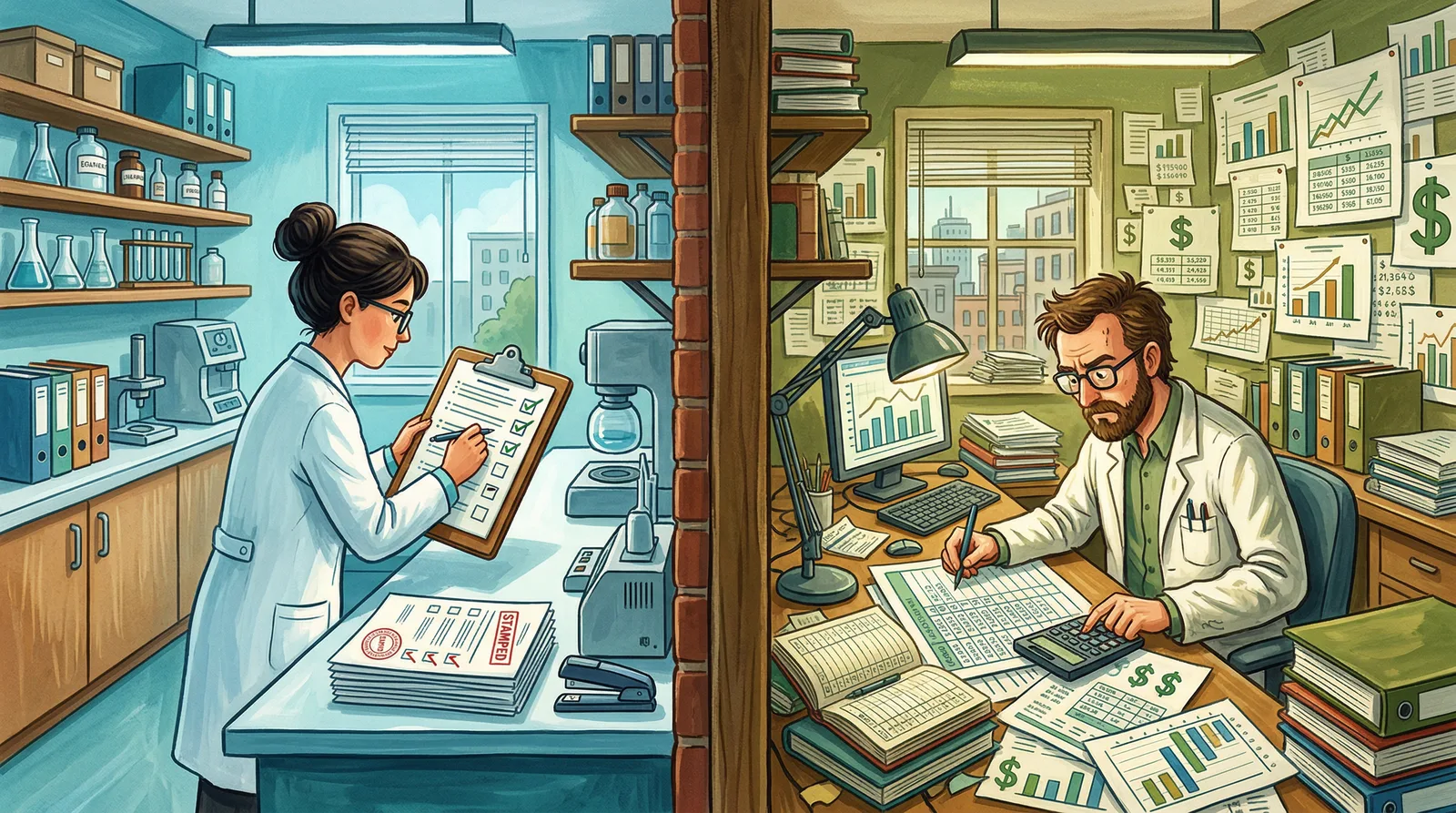
Compliance Testing
"Does the control work?"
- Tests controls
- Binary result: yes/no
- Policy-focused
- Also called "tests of controls"
Substantive Testing
"Is the data accurate?"
- Tests data/transactions
- Quantitative analysis
- Accuracy-focused
- Verifies completeness & integrity
ISACA tests the inverse relationship: strong compliance results → less substantive testing needed. But the real trap is confusing what each test does. "Does the backup run every night?" = compliance test (is the control working?). "Is the backed-up data complete and restorable?" = substantive test (is the data accurate?). If the question says "verify the control operates effectively" → compliance. If it says "verify data integrity" → substantive.
During the HealthCare.gov launch disaster in 2013, compliance tests showed the system met security policy requirements on paper. But substantive testing of actual load capacity and data integrity was inadequate — and the site crashed on launch day under real-world load, failing 600,000 users in the first week and requiring hundreds of millions in emergency remediation.
Sampling Methods
Alex stares at the database: 50,000 access log entries from last quarter. She can't review them all. She could pick randomly (statistical), target the suspicious-looking ones (judgmental), or take every 100th record (systematic). Each method has tradeoffs. "Choose based on your objective," her senior says. "If you need to project results to the whole population, go statistical."
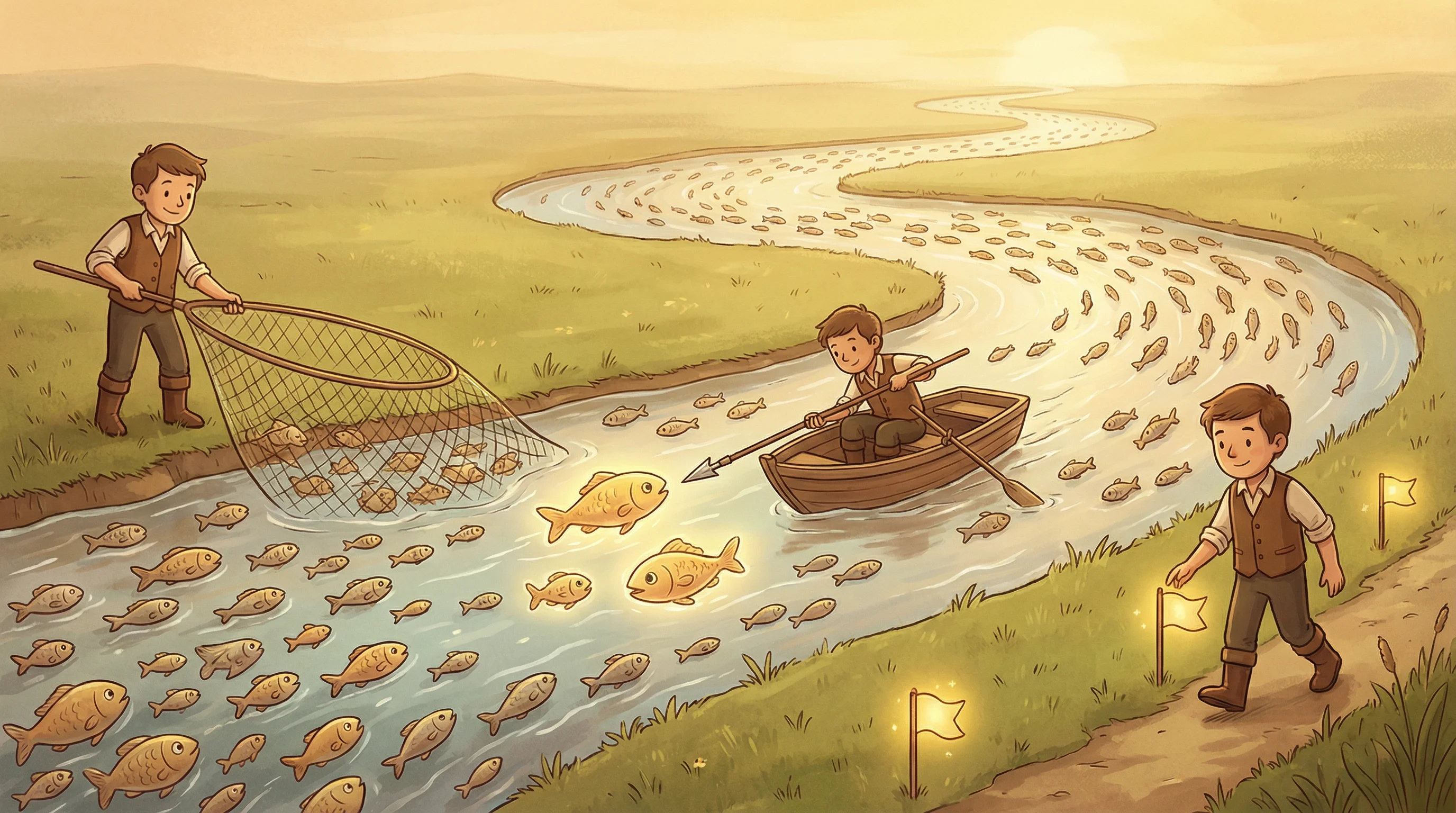
Statistical Sampling
- Mathematical basis
- Projectable to population
- Quantifies sampling risk
Methods: Random, Systematic, Stratified
Non-Statistical Sampling
- Judgment-based
- Not projectable to population
- Cannot quantify sampling risk
Methods: Haphazard, Block, Judgmental
Sampling Type by Testing Purpose
Attribute Sampling
Used for compliance testing (yes/no)
Variable Sampling
Used for substantive testing (amounts)
ISACA trap: "Statistical sampling is always superior." Wrong. Judgmental (non-statistical) sampling is appropriate when the auditor's expertise can identify high-risk items more effectively than random selection. But if the question asks about projecting results to the entire population or quantifying sampling risk — only statistical sampling can do that. Also remember: attribute sampling → compliance (yes/no, pass/fail), variable sampling → substantive (dollar amounts).
The Olympus Corporation accounting fraud ($1.7 billion hidden losses) persisted for 13 years partly because auditors used judgmental sampling that conveniently avoided the suspicious transactions. When your sampling method has blind spots, fraud hides in exactly those gaps.
Reveal Answer
Reveal Answer
Reveal Answer
She knows how to test. Now she needs to know what counts as proof.
Evidence Collection
Evidence Collection Techniques
The IT manager smiles reassuringly. "Trust me, the backups run every night. We've never had an issue." Alex writes it down but knows this is the weakest form of evidence — verbal assurance from the person being audited. She needs the backup logs, a test restore, and confirmation from the monitoring system. Proof, not promises.

Review
Examine documents, policies, logs, and records
Observation
Watch processes in action and note behaviors
Inquiry
Interview people — ask questions and get responses
Re-performance
Repeat procedures independently to verify results
CAATs
Computer-assisted audit techniques for automated testing
Most Reliable Evidence
- External sources
- Original documents
- Auditor-obtained (direct)
- Objective/quantitative
Least Reliable Evidence
- Internal sources
- Verbal/oral statements
- Auditee-provided
- Subjective/qualitative
From strongest to weakest, think: "I trust the outsider. I trust what I got myself. I somewhat trust what you gave me. I barely trust what you told me."
- 1. External independent sources — bank confirmations, third-party reports (strongest)
- 2. Auditor-obtained documentary — logs you pulled yourself, screenshots you took
- 3. Entity-provided documentary — documents management handed you
- 4. Oral evidence — "trust me, the backups run every night" (weakest)
When ISACA asks "which evidence is MOST reliable?" — rank it: external independent sources beat auditor-obtained documents, which beat entity-provided documents, which beat oral statements. The trap: a question might offer "verbal confirmation from the CFO" alongside "system-generated log." The log wins every time — even though the CFO outranks the system. Reliability comes from independence and objectivity, not authority.
Wirecard's €1.9 billion fraud persisted for years because EY accepted Wirecard-provided documents instead of independently confirming balances with the banks directly. When an independent audit was finally done, the banks denied any relationship with Wirecard existed.
Reveal Answer
Reveal Answer
Reveal Answer
Enjoying this? All 5 domains are completely free. If this helps your study, share it with someone else preparing for CISA.
She has the evidence. But reviewing it manually will take weeks.
Audit Data Analytics
CAATs & Continuous Auditing
Alex has been manually checking access logs for two days and she's only through 200 of 50,000 records. Then a colleague shows her Generalized Audit Software. She loads all 50,000 records, writes a query for anomalies, and in twelve seconds gets a complete list of every after-hours login by terminated employees. Two days of work, done in seconds.
Test Data
Dummy transactions through live or copy system
ITF
Integrated Test Facility — test in live production
Parallel Simulation
Reprocess data through auditor's model
Embedded Modules
Audit code built into production systems
GAS
Generalized Audit Software (ACL/IDEA)
Remember: "GEP IT"
- Generalized Audit Software (GAS) — analyse large data sets (ACL, IDEA)
- Embedded Audit Modules — built into production systems, always-on monitoring
- Parallel Simulation — re-process data independently through auditor's model
- Integrated Test Facility (ITF) — test data through the LIVE system (risky!)
- Test Data — dummy transactions to test controls (can use live or copy of system)
Continuous Auditing
Performed by auditors. Uses automated tools for ongoing assurance.
Continuous Monitoring
Performed by management. Real-time oversight of controls and operations.
Emerging Technologies
- AI / Machine Learning
- Data Analytics
- Robotic Process Automation (RPA)
- Blockchain Auditing
ISACA loves testing who owns what: Continuous auditing = auditors. Continuous monitoring = management. If the question asks "who is responsible for continuous monitoring?" and "IS auditor" is an option, it's a trap. Also: test data uses DUMMY transactions (not real ones). ITF runs test data through the LIVE system (risky — must remove test results after). Parallel simulation is the safest CAAT because it uses a copy of the data, not the live system.
JPMorgan's $6.2 billion London Whale trading loss (2012) stemmed partly from traders manually overriding the VaR model in Excel spreadsheets — a risk that automated, continuous monitoring tools would have detected far earlier. The VaR limits were breached over 300 times before anyone escalated.
Reveal Answer
Reveal Answer
Reveal Answer
Twelve seconds instead of two weeks. Now she needs to write up what she found — and make it stick.
Reporting & Communication
Anatomy of an Audit Report
Alex writes her first audit finding: "The server room is insecure." The IT manager pushes back: "That's just your opinion." Her senior teaches her the bulletproof formula — Condition, Criteria, Cause, Effect. She rewrites: unlocked door, policy requires badge access, reader never installed, anyone can reach production servers. Now it's not an opinion. It's a fact.

The Audit Finding Formula: Condition, Criteria, Cause & Effect
- Condition — What is (current state)
- Criteria — What should be (standard)
- Cause — Why it happened (root cause)
- Effect — The impact (consequence)
ISACA loves asking which component is missing from a finding. If it says "passwords are weak" without referencing a policy standard — the missing element is Criteria. Condition = what you found. Criteria = what it should be. Cause = why. Effect = so what. If ANY of the four is missing, the finding is incomplete. Also: always present findings to management before the final report — but independence violations go straight to the audit committee, not management.
The OPM (Office of Personnel Management) breach in 2015 exposed 21.5 million government employees' security clearance records. Audit reports had flagged OPM's weak security for years, but the findings were vague and lacked the Condition-Criteria-Cause-Effect structure needed to compel action. Management ignored them until it was too late.
Reveal Answer
Reveal Answer
Reveal Answer
The report is written. But is the audit itself any good?
Quality Assurance
Audit Quality Framework
Alex submits her draft report, proud of her work. The peer reviewer sends it back with three errors: a misattributed control owner, an incorrect risk rating, and a finding that lacked sufficient evidence. Alex's first instinct is embarrassment — but her senior smiles. "This is the system working. QA catches what you miss. That's the whole point."

Internal QA
- Ongoing reviews
- Workpaper QA
- Peer review
- Standards compliance
External QA
- Periodic assessment
- Independent review
- Benchmarking
- ISACA conformance
Improvement
- KPI tracking
- Lessons learned
- Training programs
- Process optimization
Quality Assurance Flow
When ISACA asks "what is the PRIMARY purpose of a QA review?" — the answer is conformance with standards, not "finding errors in the report." QA is about the audit process itself, not the auditee. Also watch for: "Who should perform the external QA review?" — it must be someone independent of the audit function. If the CAE (Chief Audit Executive) selects the reviewer, that compromises independence.
After Arthur Andersen's role in the Enron scandal, the Sarbanes-Oxley Act (2002) created the PCAOB specifically to perform external quality assurance reviews of audit firms. The lesson: auditors who audit themselves without external oversight eventually stop catching their own mistakes.
Reveal Answer
Reveal Answer
Reveal Answer
Alex submits her first audit report.
Three weeks. Forty-seven systems. One clean, well-structured audit report with four findings, each with Condition, Criteria, Cause and Effect. Her senior reads it and nods. "Not bad for your first week." Alex knows she got lucky on a few things. But she also knows the framework now. And the framework is what makes an auditor.
Top 10 Exam Traps — Domain 1
✓ FIRST always means: understand the business/risk environment
✓ CSA supplements audit; auditor facilitates, never evaluates
✓ Detective controls are correct when prevention isn't feasible
✓ Auditor only controls DETECTION risk
✓ Weakest form; always seek documentary or external confirmation
✓ Independence violations go to the AUDIT COMMITTEE
✓ Test data uses DUMMY transactions through the live system
✓ Compliance testing checks if controls WORK; substantive testing checks data
✓ Judgmental is appropriate when expertise can identify high-risk items
✓ Board or AUDIT COMMITTEE approves it — management approval compromises independence
Alex's story continues. Domain 2: Meridian Corp has no IT governance framework. Domain 3: a developer says "we're doing Agile" but can't show a sprint record. All 5 domains are free.